What is God Crypt v1.0 ransomware? And how does it carry out its attack?
God Crypt v1.0 ransomware, also known as Godsomware, is a file-encrypting virus designed to encrypt important data in an infected computer. It seems like it’s trying to imitate the infamous WannaCry ransomware based on its GUI. According to security experts, it does not really encrypt files. However, you must not take it lightly as its developers could update this threat anytime.
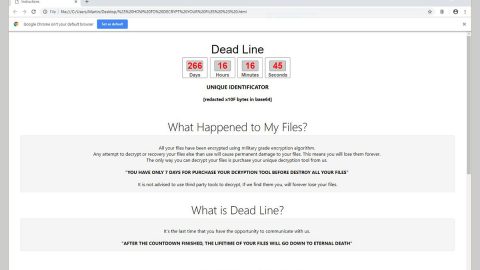
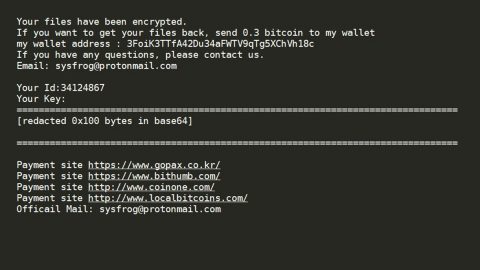
Once it infiltrates a computer, God Crypt v1.0 ransomware will drop its malicious payload in the system, download, and create malicious components in order to carry out its attack. It also modifies some registry keys and entries in the Windows Registry to allow it to run on every startup. After that, it displays a program window that is quite identical to WannaCry ransomware and changes the desktop wallpaper of the infected computer. Here’s the ransom note displayed in the program window:
“Ooops, your files have been encrypted!
What Happened to My Computer?
Your important files are encrypted.
Many of your documents, photos, videos, databases, and other files are no longer
accessible because they have been encrypted. Maybe you are busy looking for a way to
recover your files but do not waste your time. Nobody can recover your files without
our decryption service.
Can I Recover My Files?
Sure. We guarantee that you can recover all your files safely and easily. But you have
not so enough time.
You can decrypt some of your files for free. Try now by clicking.
But if you want to decrypt all your files, you need to pay.
You only have 3 days to submit the payment. After that, the price will be doubled.
Also, if you don’t pay in 7 days, you won’t be able to recover your files forever.
We will have free events for users who are so poor that they couldn’t pay in 6 months.
How Do I Pay?
Payment is accepted in Bitcoin only. For? more information, Click.
Please check the current price of Bitcoin and buy some bitcoins. For more information,
click ( How to buy bitcoins ).”
How does God Crypt v1.0 ransomware proliferate?
Like other crypto-malware, God Crypt v1.0 ransomware proliferate using spam emails. Cyber crooks usually attach malware-laden attachments to emails and send them to users using spambots. The attachment could be a PDF file, ZIP file, or a document with macro scripts used to launch God Crypt v1.0 ransomware in the system. And so whenever a suspicious-looking email finds its way into your inbox, you must double-check its content before you download its attachment and whatnot.
To wipe out God Crypt v1.0 ransomware from your computer, you need to use the following removal guide.
Step_1: Type 29b579fb811f05c3c334a2bd2646a27a in the program window to close it and have it disabled.
Step_2: Next, tap Ctrl + Shift + Esc keys to open the Task Manager and then go to the Processes and look for the malicious process of God Crypt v1.0 ransomware named “Godsomware.exe” then right-click on it and select End Process or End Task.
Step_3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step_4: Look for dubious programs that might be related to God Crypt v1.0 ransomware and then Uninstall it/them.
Step_5: Tap Win + E to launch File Explorer.
Step_6: After opening File Explorer, navigate to the following directories below and look for malicious components of God Crypt v1.0 ransomware such as Godsomware.exe and remove them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step_7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_8: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_9: Navigate to the listed paths below and look for the registry keys and sub-keys created by God Crypt v1.0 ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_10: Delete the registry keys and sub-keys created by God Crypt v1.0 ransomware.
Step_11: Close the Registry Editor.
Step_12: Empty your Recycle Bin.
Restore the previous state of your files using the Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if God Crypt v1.0 ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Congratulations, you have just removed God Crypt v1.0 Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove God Crypt v1.0 Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
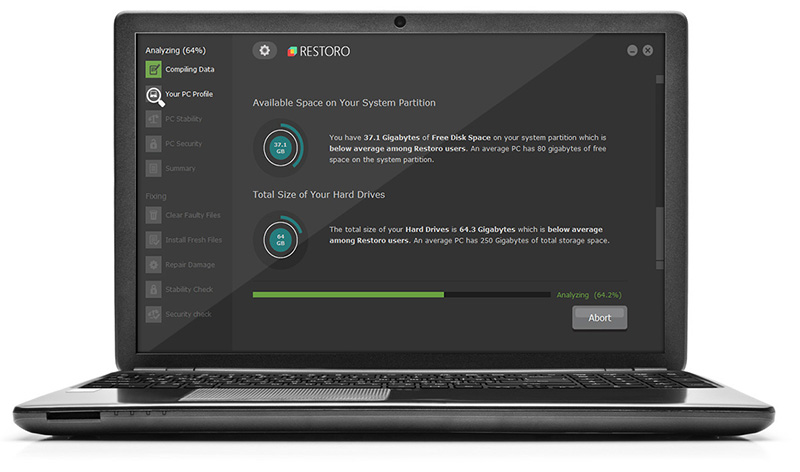
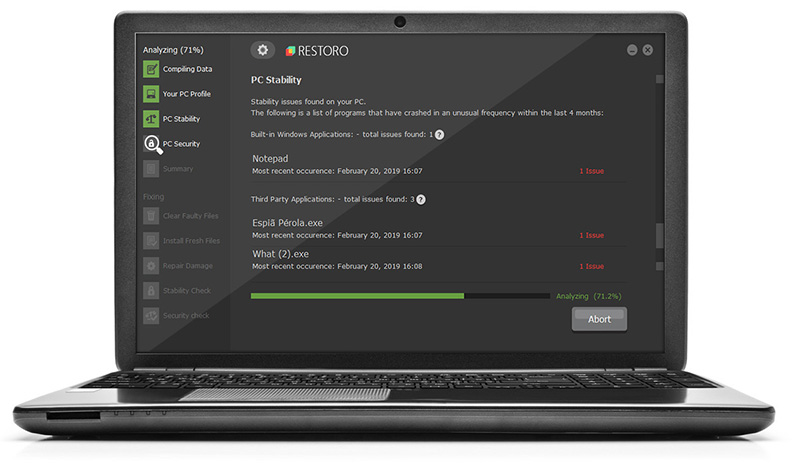
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.