What is FilesLocker v2.0 ransomware? And how does it carry out its attack?
FilesLocker v2.0 ransomware is a file-encrypting malware that happens to be a new variant of FilesLocker ransomware which was first released in October 2018. And now it seems that its developers decided to modify the crypto-malware to create an improved variant, hence, FilesLocker v2.0 ransomware. It still uses the same encryption algorithm in locking files which is AES although the extension it now uses is a different one,”.[[email protected]]”.
Once it carries out its attack, FilesLocker v2.0 ransomware will drop its malicious payload in the system, “Installer.exe”, which obviously is disguised as an installer for some program. After this malicious payload is executed, FilesLocker v2.0 ransomware gets installed in the system. It then connects the infected computer to a remote Command and Control server where it downloads its other components and places them on system folders. These malicious components are used for the data gathering and stealth protection modules. In the first module, it collects data in the system which is used for the second module.
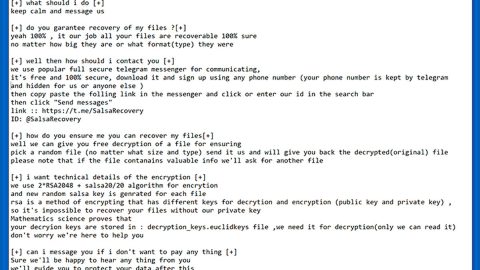
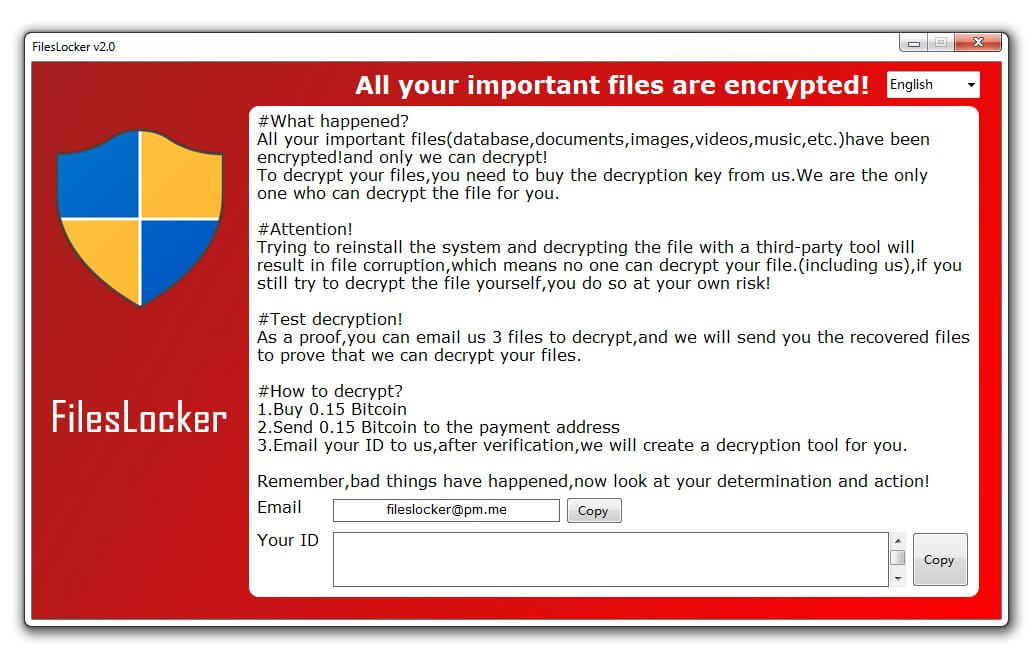
The stealth protection module scans the computer for strings of security and antivirus programs installed in the system and when it finds them, the crypto-malware either disables them or removes them. After that, it creates modifications in the Windows Registry to allow it to run automatically on every system boot. Following these system changes, FilesLocker v2.0 ransomware will start the encryption using the AES cipher and appends the “.[[email protected]]” extension to the affected files. Once the encryption is completed, it opens a program window that contains the following ransom note:
“FilesLocker v2.0
All your important files are encrypted!
#What happened?
All your important files(database,documents,images,videos,music,etc.)have been encrypted!and only we can decrypt!
To decrypt your files, you need to buy the decryption key from us. We are the only ones who can decrypt the file for you.
#Attention!
Trying to reinstall the system and decrypt the file with a third-party tool will result in file corruption, which means no one can decrypt your file. (including us),if you still try to decrypt the file yourself, you do so at your own risk!
#Test decryption!
As proof, you can email us 3 files to decrypt, and we will send you the recovered files to prove that we can decrypt your files.
#How to decrypt?
1. Buy 0.15 Bitcoin
2. Send 0.15 Bitcoin to the payment address
3. Email your ID to us, after verification, we will create a decryption tool for you.
Remember, bad things have happened, now look at your determination and action!”
How does FilesLocker v2.0 ransomware proliferate?
FilesLocker v2.0 ransomware proliferates the same way as its predecessor which is via malicious spam email campaigns. Creators attach a malicious executable file (Installer.exe) in emails and send them to targeted users or random users using spam bot.
Follow the removal instructions laid out below to eliminate FilesLocker v2.0 ransomware from your computer.
Step_1: Reboot your computer and boot it into Safe Mode with Command Prompt by pressing F8 a couple of times until the Advanced Options menu appears.
Step_2: Navigate to Safe Mode with Command Prompt using the arrow keys on your keyboard. After selecting Safe Mode with Command Prompt, hit Enter.
Step_3: After loading the Command Prompt type cd restore and hit Enter.
Step_4: After cd restore, type in rstrui.exe and hit Enter.
Step_5: A new window will appear, and then click Next.
Step_6: Select any of the Restore Points on the list and click Next. This will restore your computer to its previous state before being infected with the FilesLocker v2.0 Ransomware. A dialog box will appear and then click Yes.
Step_7: After System Restore has been completed, try to enable the disabled Windows services.
- Press Win + R keys to launch Run.
- Type in msc in the box and press Enter to open Group Policy.
- Under Group Policy, navigate to:
- User Configuration\Administrative Templates\System
- After that, open Prevent access to the command prompt.
- Select Disable to enable cmd
- Click the OK button
- After that, go to:
- Configuration\Administrative Templates\System
- Double click on the Prevent Access to registry editing tools.
- Choose Disabled and click OK.
- Navigate to :
- User Configuration\Administrative Templates\System>Ctrl+Alt+Del Options
- Double click on Remove Task Manager.
- And then set its value to Disabled.
Step_8: Open Task Manager by pressing Ctrl + Shift + Esc at the same time. Proceed to the Processes tab and look for the malicious processes of FilesLocker v2.0 ransomware such as Installer.exe, SF.exe, TR.exe, or BLACKROUTER.exe and end them all.
Step_9: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK to open the list of installed programs. From there, look for FilesLocker v2.0 ransomware or any malicious program and then Uninstall it.
Step_10: Tap Windows + E keys to open the File Explorer then navigate to the following directories and delete the malicious files created by FilesLocker v2.0 ransomware such as #DECRYPT MY FILES # .txt, # 解密 我 的 文件 # .txt, Windows update.exe, 5b88484028ab1.pnq, Installer.exe, and other suspicious-looking files.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %TEMP%
Step_11: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use Restoro this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_12: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_13: Navigate to the paths listed below and delete all the registry values added by FilesLocker v2.0 ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_14: Close the Registry Editor and empty your Recycle Bin.
Congratulations, you have just removed FilesLocker v2.0 Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove FilesLocker v2.0 Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
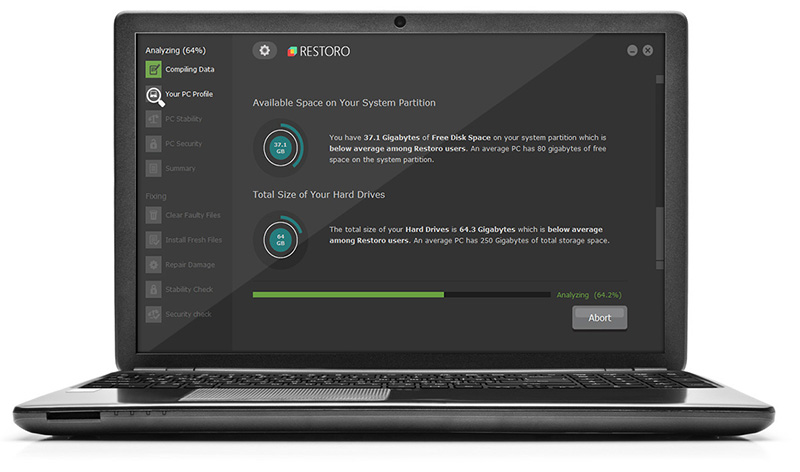
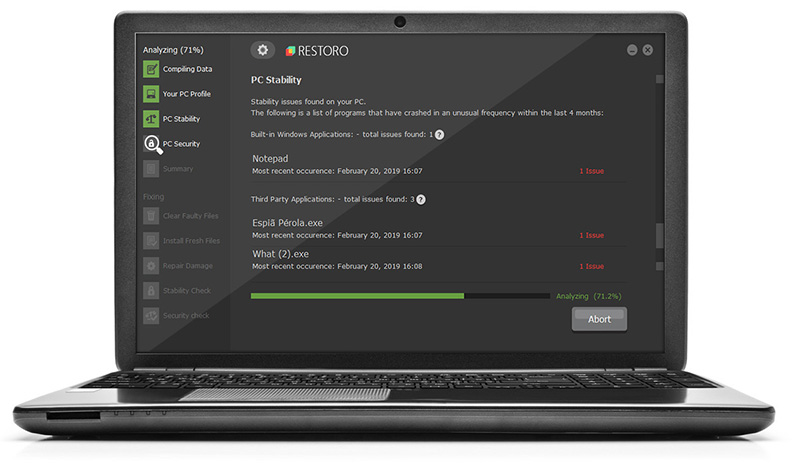
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.