What is Buran ransomware? And how does it work?
Buran ransomware is a file-encrypting virus created to lock important data in a computer. It uses random letters and numbers as its extension in marking the compromised files which seems to be the same as the unique ID given to the victims. This new crypto-virus was discovered by Michael Gillespie and was spotted by a security researcher named “nao_sec” in a malvertising campaign that redirects potential victims to the RIG Exploit kit.
According to security experts, the appendix used by this ransomware looks like a Globally Unique Identifier or GUID and is added to every encrypted file. The instant it infects a targeted machine, Buran ransomware will establish a connection to a remote C&C server controlled by the attackers. This is where it downloads additional components. The downloaded components are then placed on system folders in order to launch and repress system processes.
It also employs a data gathering module to collect sensitive data in the system as well as the stealth protection module to use the gathered data to evade security and antivirus programs installed in the computer that could interfere with its attack. In addition, it also alters some registry keys and sub-keys like Run and RunOnce so that it can run automatically in every system boot.
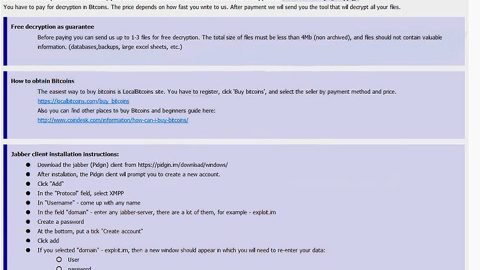
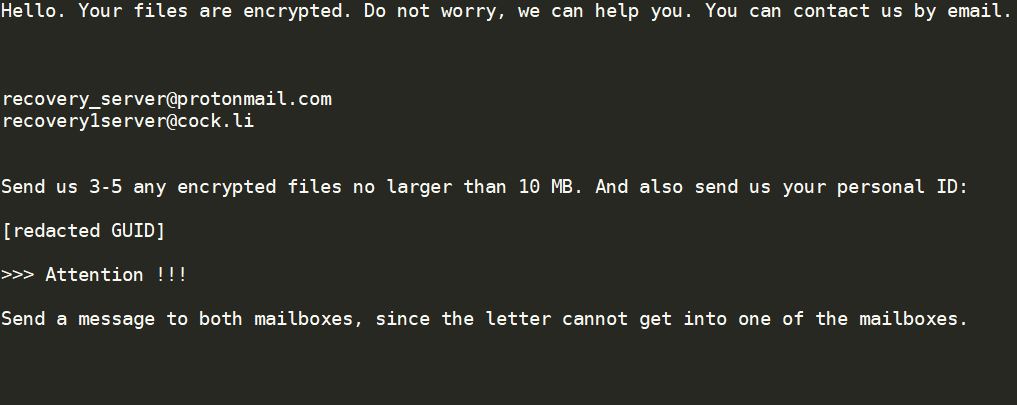
After it completes modifying system settings, Buran ransomware will begin encrypting important files in the system using a sophisticated encryption algorithm. Following file encryption, it adds the random characters to every affected file and opens a text file named “!!! YOUR FILES ARE ENCRYPTED !!!.txt” that contains the following message:
“!!! YOUR FILES ARE ENCRYPTED !!!
All your files, documents, photos, databases, and other important
files are encrypted.
You are not able to decrypt it by yourself! The only method
of recovering files is to purchase a unique private key.
Only we can give you this key and only we can recover your files.
To be sure we have the decryptor and it works you can send an
email [email protected] and decrypt one file for free. But this
file should be of not valuable!
Do you really want to restore your files?
Write to email [email protected], [email protected]
Your personal ID: –
Attention!
* Do not rename encrypted files.
* Do not try to decrypt your data using third-party software,
it may cause permanent data loss.
* Decryption of your files with the help of third parties may
cause increased price (they add their fee to our) or you can
become a victim of a scam.”
How does Buran ransomware spread over the web?
Like pointed out, Buran ransomware spreads the web using the RIG exploit kit. You can get redirected to this exploit kit online when you click on some link online. Aside from that, it could also spread via deceptive downloads, fake updates, exploit kits. It may also spread using malicious email attachments. These attachments may be PDF files, ZIP files, or documents with macro scripts used to install Buran ransomware in the system.
Eliminate Buran ransomware from your compromised computer by following the removal instructions laid out below.
Step_1: First, restart your computer and boot into Safe Mode with Command Prompt by tapping the F8 key a couple of times until the Advanced Options menu appears.
Step_2: Navigate to Safe Mode with Command Prompt using the arrow keys on your keyboard. After selecting Safe Mode with Command Prompt, hit Enter.
Step_3: After loading the Command Prompt type cd restore and hit Enter.
Step_4: After cd restore, type in rstrui.exe and hit Enter.
Step_5: A new window will appear, and then click Next.
Step_6: Select any of the Restore Points on the list and click Next. This will restore your computer to its previous state before being infected with Buran Ransomware. A dialog box will appear and then click Yes.
Step_7: After System Restore has been completed, try to enable the disabled Windows services.
- Press Win + R keys to launch Run.
- Type in msc in the box and press Enter to open Group Policy.
- Under Group Policy, navigate to:
- User Configuration\Administrative Templates\System
- After that, open Prevent access to the command prompt.
- Select Disable to enable cmd
- Click the OK button
- After that, go to:
- Configuration\Administrative Templates\System
- Double click on the Prevent Access to registry editing tools.
- Choose Disabled and click OK.
- Navigate to :
- User Configuration\Administrative Templates\System>Ctrl+Alt+Del Options
- Double click on Remove Task Manager.
- And then set its value to Disabled.
Step_8: Open Task Manager by pressing Ctrl + Shift + Esc at the same time. Proceed to the Processes tab and look for the malicious processes of Buran Ransomware and end them all.
Step_9: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK to open the list of installed programs. From there, look for Buran ransomware or any malicious program and then Uninstall it.
Step_10: Tap Windows + E keys to open the File Explorer then navigate to the following directories and delete the malicious files created by Buran ransomware like “!!! YOUR FILES ARE ENCRYPTED !!!.txt”, “EDILI INDUSTRIA.pdf.3674AD9F-59F0F56A8885EA”, and “[random].exe”.
- %UserProfile%\AppData
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
- %TEMP%.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step_11: Close the File Explorer.
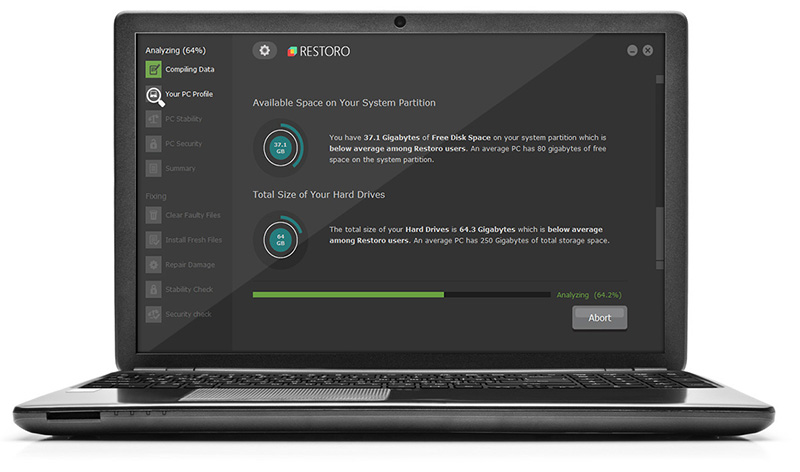
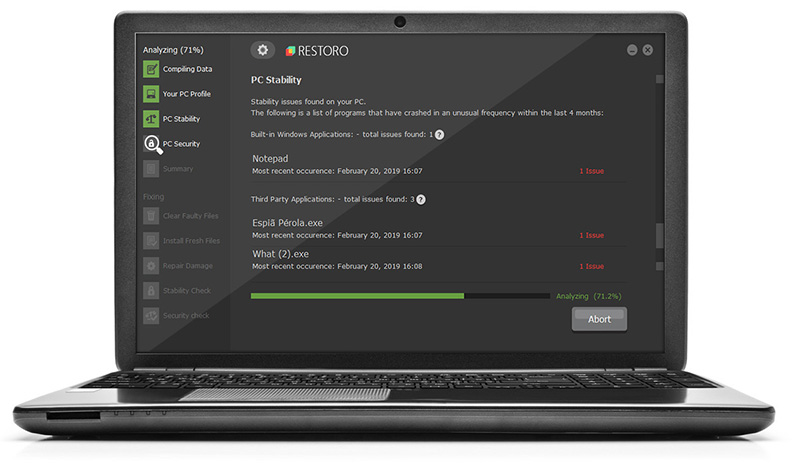
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_12: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_13: Navigate to the paths listed below and delete all the registry values added by Buran ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_14: Close the Registry Editor and empty your Recycle Bin.
Congratulations, you have just removed Buran Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove Buran Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.