What is GandCrab2 ransomware? And how does it implement its attack?
GandCrab2 ransomware is a new version of the notorious GandCrab ransomware. Just last week, a security firm known as Bitdefender, the Romanian Police was able to allegedly access the Command and Control servers of GandCrab ransomware which allowed them to recover decryption keys for victims. Right after this breach, developers of the dangerous ransomware stated that they would release another version of their ransomware that would include a more secure command and control server to prevent the same thing from happening. And as it turns out, these cyber crooks made good on their promise as a new version called GandCrab2 was released.
The hostnames for this ransomware’s Command and Control servers were one of the biggest notable changes that its developers have made. The hostnames are “politiaromana.bit” which is obviously named after the Romanian Police who helped in recovering the decryption keys. Aside from that, crooks also change the extension used in marking the encrypted files as well as the ransom note names. The extension used is now .CRAB which is appended at the end of an encrypted file’s name.
During the implementation of its attack, GandCrab2 ransomware still targets the same file types as the original GandCrab ransomware – some of which are as follows:
1cd, .3dm, .3ds, .3fr, .3g2, .3gp, .3pr, .7z, .7zip, .aac, .ab4, .abd, .acc, .accdb, .accde, .accdr, .accdt, .ach, .acr, .act, .adb, .adp, .ads, .agdl, .ai, .aiff, .ait, .al, .aoi, .apj, .apk, .arw, .ascx, .asf, .asm, .asp, .aspx, .asset, .asx, .atb, .avi, .awg, .back, .backup, .backupdb, .bak, .bank, .bay, .bdb, .bgt, .bik, .bin, .bkp, .blend, .bmp, .bpw, .bsa, .c, .cash, .cdb, .cdf, .cdr, .cdr3, .cdr4, .cdr5, .cdr6, .cdrw, .cdx, .ce1, .ce2, .cer, .cfg, .cfn, .cgm, .cib, .class, .cls, .cmt, .config, .contact, .cpi, .cpp, .cr2, .craw, .crt, .crw, .cry, .cs, .csh, .csl, .css, .csv, .d3dbsp, .dac, .das, .dat, .db, .db_journal, .db3, .dbf, .dbx, .dc2, .dcr, .dcs, .ddd, .ddoc, .ddrw, .dds, .def, .der, .des, .design, .dgc, .dgn, .dit, .djvu, .dng, .doc, .docm, .docx, .dot, .dotm, .dotx, .drf, .drw, .dtd, .dwg, .dxb, .dxf, .dxg, .edb, .eml, .eps, .erbsql, .erf, .exf, .fdb, .ffd, .fff, .fh, .fhd, .fla, .flac, .flb, .flf, .flv, .flvv, .forge, .fpx, .fxg, .gbr, .gho, .gif, .gray, .grey, .groups, .gry, .h, .hbk, .hdd, .hpp, .html, .ibank, .ibd, .ibz, .idx, .iif, .iiq, .incpas, .indd, .info, .info_, .ini, .iwi, .jar, .java, .jnt, .jpe, .jpeg, .jpg, .js, .json, .k2p, .kc2, .kdbx, .kdc, .key, .kpdx, .kwm, .laccdb, .lbf, .lck, .ldf, .lit, .litemod, .litesql, .lock, .log, .ltx, .lua, .m, .m2ts, .m3u, .m4a, .m4p, .m4v, .ma, .mab, .mapimail, .max, .mbx, .md, .mdb, .mdc, .mdf, .mef, .mfw, .mid, .mkv
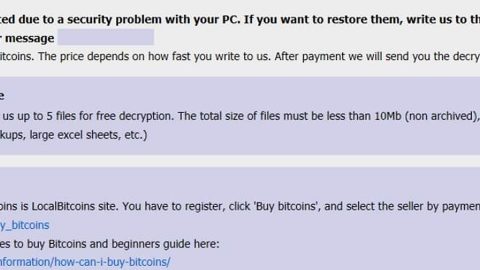
Right after the encrypting using the same encryption algorithm, GandCrab2 ransomware drops its ransom note named “CRAB-Decrypt.txt” that states:
“—= GANDCRAB =—
Attention!
All your files documents, photos, databases and other important files are encrypted and have the extension: .GDCB
The only method of recovering files is to purchase a private key. It is on our server and only we can recover your files.
The server with your key is in a closed network TOR. You can get there by the following ways:
- Download Tor browser – https://www.torproject.org/
- Install Tor browser
- Open Tor Browser
- Open link in tor browser: http://gdcbmuveqjsli57x.onion/[id]
- Follow the instructions on this page
On our page, you will see instructions on payment and get the opportunity to decrypt 1 file for free.
If you can’t download TOR and use it, or in your country, TOR blocked, read it:
- Visit https://tox.chat/download.html
- Download and install qTOX on your PC.
- Open it, click “New Profile” and create a profile.
- Search our contact – 6C5AD4057E594E090E0C987B3089F74335DA75F04B7403E0575663C26134956917D193B195A5
- In message please write your ID and wait our answer: 6361f798c4ba3647
DANGEROUS!
Do not try to modify files or use your own private key – this will result in the loss of your data forever!”
How does GandCrab2 ransomware proliferate?
Just like the previous one, this new version proliferates through a malvertising campaign called Seamless which pushes the visitors to the RIG exploit kit. After that, this exploits it will attempt to take advantage of the vulnerabilities in the visitor’s software so crooks can install GandCrab2 ransomware into their computer.
Refer to the following removal guide to terminate GandCrab2 ransomware from your system.
Step 1: Close the ransom note and the TOR payment page of GandCrab2 ransomware and then tap Ctrl + Shift + Esc keys to open the Task Manager.

Step 2: After opening the Task Manager, look for the following malicious processes of GandCrab2 ransomware, click on each one of them and select End Process or End Task.
msftesql.exe, sqlagent.exe, sqlbrowser.exe, sqlservr.exe, sqlwriter.exe, oracle.exe, ocssd.exe, dbsnmp.exe, synctime.exe, mydesktopqos.exe, agntsvc.exeisqlplussvc.exe, xfssvccon.exe, mydesktopservice.exe, ocautoupds.exe, agntsvc.exeagntsvc.exe, agntsvc.exeencsvc.exe, firefoxconfig.exe, tbirdconfig.exe, ocomm.exe, mysqld.exe, mysqld-nt.exe, mysqld-opt.exe, dbeng50.exe, sqbcoreservice.exe, excel.exe, infopath.exe, msaccess.exe, mspub.exe, onenote.exe, outlook.exe, powerpnt.exe, steam.exe, thebat.exe, thebat64.exe, thunderbird.exe, visio.exe, winword.exe, wordpad.exe

Step 3: Close the Task Manager and then open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for GandCrab2 ransomware or any suspicious program and then Uninstall it/them.

Step 5: Tap Win + E to launch File Explorer.
Step 6: After opening File Explorer, navigate to the following locations below and look for GandCrab2 ransomware’s malicious components and delete them all.
- %TEMP%
- %APPDATA%
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step 7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the following paths:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI\Background
- HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Personalization
- HKEY_CURRENT_USER\Control Panel\Desktop\ScreenSaveTimeOut
- HKEY_CURRENT_USER\Control Panel\Desktop
Step 10: Under the paths listed above, look for registry values created by GandCrab2 ransomware and delete it. Close the Registry Editor then empty the Recycle Bin.
You have to make sure that GandCrab2 ransomware is completely terminated from your system. To do that, follow the advanced removal steps below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. The installation will start automatically once a download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.