What is Crystalcrypt Ransomware? And how does it work?
Crystalcrypt ransomware is new cyber infection that encrypts files to make them inaccessible. This ransomware seems to be a different variant of the Lightningcrypt ransomware. Crystalcrypt is a real threat to small businesses and computer users’ data, web servers, databases, etc. It uses an executable file named zSd73pPjhvxBTTMtbRwO.exe to infiltrate your computer system. After that, it scans your computer for different file types listed below:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks,.jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
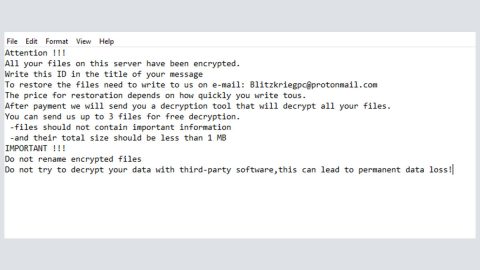
It then encrypts your file by appending the .BLOCKED file extension on the targeted files. It also drops several files in your computer like the CrystalCrypt_Recover_Instructions.png which will replace your desktop background and the Crystalcrypt_uniqueid.txt which contains your unique id that will be used when recovering your files and then the CrystalCrypt_Recover_Instructions.txt that contains the following message:
‘You became a victim of the CrystalCrypt Ransomware!
All your files have been encrypted
For each try to do anything I will delete files
Pay 0.17 Bitcoins on ‘Blockchain.info’
Send your uniqe ID in the description of the Bitcoin payment
You can find them on your desktop in ‘crystalcrypt_uniqeid.txt’
After the payment your files will be decrypted!
Have fun ;)_
PAY 0.17 Bitcoins to : [BITCOIN ADDRESS]’
How is Crystalcrypt ransomware distributed?
Although Crystalcrypt ransomware uses exploit kits, Trojans, malvertising or fake ads to infect your computer, it mainly makes use of spam emails with corrupted attachment. Spam emails are one of the distribution methods commonly used by cyber criminals to deploy their infected files in order to infiltrate your computer. that’s why you have to make sure you double check the sender especially if it’s an unknown one before you open or download the attachments.s
Follow the removal guide below to eliminate Crystalcrypt ransomware:
Step 1: Open Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.

Step 2: Go to the Processes tab and look for any suspicious processes and then kill them.

Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 4: Look for Crystalcrypt ransomware or any suspicious program and then Uninstall.

Step 5: Hold down Windows + E keys simultaneously to open File Explorer.
Step 6: Go to the directories listed below:
- %USERPROFILE%/ Downloads
- %USERPROFILE%/Desktop
- %TEMP%
- %APPDATA%
Step 7: Look for Crystalcrypt’s executable file which is zSd73pPjhvxBTTMtbRwO.exe and remove ANY suspicious files you can find in the directories listed above that may be related to Crystalcrypt ransomware.
Step 8: Go to desktop and delete the files created by Crystalcrypt ransomware.
Step 9: Empty the Recycle Bin.
Step 10: Try to recover your encrypted files.
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if the Crystalcrypt Ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Follow the continued advanced steps below to ensure the removal of the Crystalcrypt ransomware:
Perform a full system scan using SpyRemover Pro.
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch SpyRemover Pro.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Pro to protect your computer from future threats.