What is Enc_robbinhood ransomware? And how does it implement its attack?
Enc_robbinhood ransomware is one of the file-encrypting threats discovered in the last week of March 2019. It stealthily infiltrates your computer and encrypts various stored data, especially the important ones, and hold them hostage in exchange for a ransom. As of the moment, there isn’t a lot of information regarding this ransomware as it is still new so the chances of getting an insight into the origin of the threat are slim.

As soon as its malicious payload is dropped in the system, Enc_robbinhood establishes a connection to a remote Command and Control or C & C server where it downloads additional components. The downloaded components are then placed on system folders in order to launch and repress system processes. It also employs a data gathering module to collect sensitive data in the system as well as the stealth protection module to use the gathered data to evade security and antivirus programs installed in the computer that could interfere with its attack. In addition, it also alters some registry keys and sub-keys like Run and RunOnce so that it can run automatically in every system boot.
After it completes modifying system settings, Enc_robbinhood ransomware will begin encrypting important files in the system using a sophisticated encryption algorithm. Following file encryption, it adds the .enc_robbinhood suffix to every affected file and opens a program window that contains the following message:
“What happened to your files?
All your files are encrypted with RSA-4096, Read more on https://en.wikipedia.org/wiki/RSA_(cryptosystem)
RSA is an algorithm used by modern computers to encrypt and decrypt data. RSA is an asymmetric cryptographic algorithm. Asymmetric means that there are two different keys. This is also called public-key cryptography because one of the keys can be given to anyone:
1 – We encrypted your files with our “Public key”
2 – You can decrypt, the encrypted files with a specific “Private key” and your private key are in our hands ( It’s not possible to recover your files without our private key )
—
Is it possible to get back your data?
Yes, We have a decrypter with all your private keys. We have two options to get all your data back.
Follow the instructions to get all your data back:
OPTION 1
Step 1: You must send us 0.8 Bitcoin(s) for each affected system
Step 2: Inform us in a panel with hostname(s) of the system you want, wait for confirmation and get your decrypter
OPTION 2
Step 1: You must send us 13 Bitcoin(s) for all affected system
Step 2: Inform us in the panel, wait for confirmation and get all your decrypters
Our Bitcoin address is: 132wg6kkJJ4MpNKnuhVoptYPmYHf6C5xHE
BE CAREFUL, THE COST OF YOUR PAYMENT INCREASES $10,000 EACH DAY AFTER THE FOURTH DAY
—
Access to the panel ( Contact us )
The panel address: http://xbt4titax4pzza6w.onion/EvcNuvq4gckb/
Alternative addresses
https://xbt4titax4pzza6w.onion.pet/EvcNuvq4gckb/
https://xbt4titax4pzza6w.onion.to/EvcNuvq4gckb/
—
Access to the panel using Tor Browser
If none of our links are accessible you can try tor browser to get in touch with us:
Step 1: Download Tor Browser from here: https://www.torproject.org/download/download.html.en
Step 2: Run Tor Browser and wait to connect
Step 3: Visit our website at the panel address
If you’re having a problem with using Tor Browser, Ask Google: how to use tor-browser
—
Wants to make sure we have your decrypter?
To make sure we have your decrypter you can upload at most 3 files (maximum size allowance is 10 MB in total) and get your data back as a demo.
—
Where to buy Bitcoin?
The easiest way is LocalBitcoins, but you can find more websites to buy bitcoin using Google Search: buy bitcoin online”
How does Enc_robbinhood ransomware proliferate?
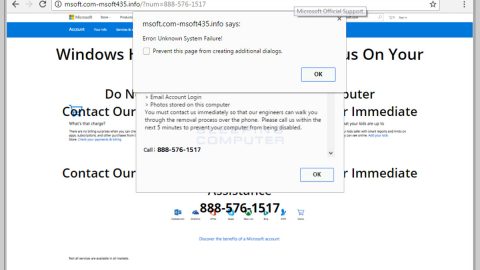
Enc_robbinhood ransomware proliferates via malicious spam emails. These kinds of emails are mostly disguised and often have a catchy subject telling users that it is an urgent matter and that the attachment must be downloaded. Enc_robbinhood ransomware either uses a ZIP file or a document file as its attachment which is used to launch its attack on the victim’s computer. To ward off these kinds of attacks it is advisable to always keep both your antivirus program and your operating system up-to-date.
Terminate Enc_robbinhood ransomware from your computer by following the removal instructions provided below.
Step_1: Close the program window of Enc_robbinhood ransomware. If you find it hard to do so, you can close it via Task Manager. Just tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step_2: Next, go to the Processes tab and look for the malicious process of Enc_robbinhood ransomware. Such processes typically consume a high amount of system resources and are named randomly so you need to beware of them. Once you found these processes, right-click on each one of them and select End Process or End Task.
Step_3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in “appwiz.cpl” and then click OK or press Enter.
Step_4: Look for dubious programs that might be related to Enc_robbinhood ransomware and then Uninstall it/them.
Step_5: Close Control Panel and then tap Win + E to launch File Explorer.
Step_6: After opening File Explorer, navigate to the following directories below
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
- C: \Documents and Settings\Administrator\Local Settings\% Temp%\****. Exe
- C: \Users\Administrator\AppData\Local\Temp\
Step_7: Now look for the malicious components of Enc_robbinhood ransomware like [random].exe and delete them.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_8: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_9: Navigate to the listed paths below and look for the registry keys and sub-keys created by Enc_robbinhood ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_10: Delete the registry keys and sub-keys created by Enc_robbinhood ransomware.
Step_11: Close the Registry Editor.
Step_12: Empty your Recycle Bin.
Try to recover your encrypted files using their Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if Enc_robbinhood ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Congratulations, you have just removed Enc_robbinhood Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove Enc_robbinhood Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
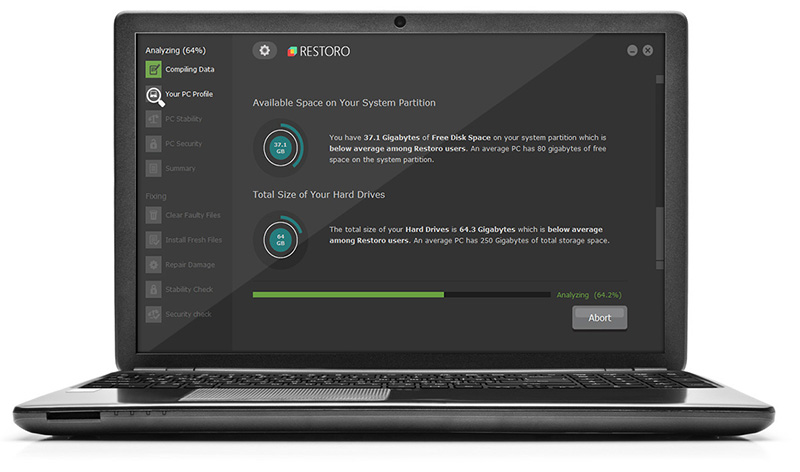
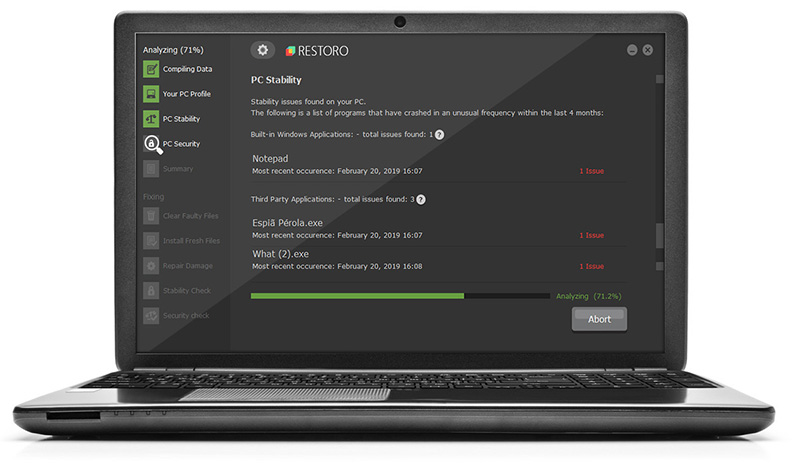
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.