What is Scarab Hitler ransomware? And how does it carry out its attack?
Scarab Hitler ransomware is a data-encrypting malware that uses AES military-grade encryption algorithm in locking its targeted files. This new Scarab variant was discovered recently and uses the .hitler extension to mark its encrypted files. It uses two email addresses such as “[email protected]” and “[email protected]”.
The moment it infects a computer, it starts to carry out its attack by dropping a malicious payload in the system. This malicious payload is the one that connects the computer to a remote Command and Control server where several malicious components of Scarab Hitler ransomware came from. It also employs a data gathering module in order to collect information about the user and the system. The harvested data and other malicious components are then used for stealth protection which prevents any security programs from interfering with Scarab Hitler ransomware’s attack.
Moreover, this crypto-malware also modifies the entries in the Windows Registry so that it can run on every system boot automatically. It usually modifies registry keys like the Run and RunOnce keys. After that, it will scan the system in search for files with specific formats. Once it finds its targeted files, it encrypts them using the AES cipher and adds the .hitler suffix to each one of the encrypted file. It then drops a file named “HOW TO RECOVER ENCRYPTED FILES.txt” which contains the following text:
“Your files are now encrypted!
Your personal identifier:
6A020000000000008FF6A8C61D915803008045B0296B3FFC69CE88FCF807B4CAC3DBA6B52E50AAB19D5964EB5DEF1D8B6C5050B9376
66AA98DCB48AB4946B75DE21EDDDCD78545BF5595DAD75598FA18976CEBA5F9762A2B647BA74B752231BDB578952E6D432AA760F1
77E8EA1658A0DDB71DBAA892E67B41B2665F12AC9DFA3B643DFDBB2632BAF95A7973E9543269FF6B5B137ACB7BBBEA2ED4CEF5678C
AEE966E9E3879DC9CB24150F899E862041B927B0802834776461305B307C7C9B7B61750C938724061B4C6648A5E86DC786B9FC54B10C
4A6B58F1CA64024C78DBDB8550FAC39B38C4A43A78FA40714C25542B2A9DD135A07C721F52E2A4AF4C9DC9D0532AEC7CF90E4730E
DDBB82193ABEAD5180878CA0A56ABDB601CBE58C9B59CD5F01B5E5BA0F7800667910CAE00F98D0586F0102117DE08DF3337027EC07
All your files have been encrypted due to a security problem with your PC.
Now you should send us an email with your personal identifier.
This email will be as confirmation you are ready to pay for the decryption key.
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us.
After payment, we will send you the decryption tool that will decrypt all your files.
Contact us using this email address:
[email protected]
Free decryption as the guarantee!
Before paying you can send us up to 3 files for free decryption.
The total size of files must be less than 10Mb (non-archived), and files should not contain
valuable information (databases, backups, large excel sheets, etc.).
Attention!
* Do not rename encrypted files.
* Do not try to decrypt your data using third party software, it may cause permanent data loss.
* Decryption of your files with the help of third parties may cause increased price
(they add their fee to our) or you can become a victim of a scam.”
If you are one of the unfortunate victims of Scarab Hitler ransomware, paying the ransom is not advised as it does not guarantee the restoration of your files. So the best thing you can do for now is to obliterate this pesky ransomware threat and wait until a free decryptor is available.
How does Scarab Hitler ransomware spread over the web?
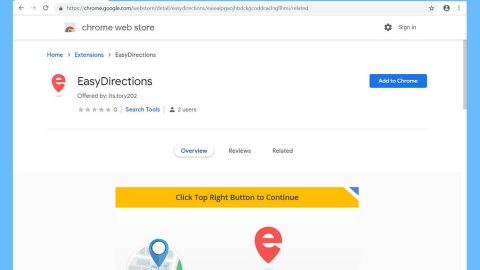
Scarab Hitler ransomware may spread the web in several ways. For one, it might use malicious spam email campaigns as well as freeware in spreading its malicious payload. Usually, crooks disguise a malware-laden email to make it look like a typical email and urge users to download and open the attachment or to click a link that redirects users to the malicious payload. Which is why you need to be more careful and watch out for any suspicious-looking emails.
For the removal of Scarab Hitler ransomware, follow the instructions given below.
Step 1: Tap the Ctrl + Alt + Delete keys to open a menu and then expand the Shutdown options which is right next to the power button.
Step 2: After that, tap and hold the Shift key and then click on Restart.
Step 3: And in the Troubleshoot menu that opens, click on the Advanced options and then go to the Startup settings.
Step 4: Click on Restart and tap F4 to select Safe Mode or tap F5 to select Safe Mode with Networking.
Step 5: After your PC has successfully rebooted, tap Ctrl + Shift + Esc to open the Task Manager.

Step 6: Go to the Processes tab and look for any suspicious-looking processes that could be related to Scarab Bin ransomware and then end their processes.

Step 7: Exit the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 8: Look for suspicious programs that could be related to Scarab Bin ransomware and then uninstall them.

Step 9: Close Control Panel and tap Win + E keys to open File Explorer.
Step 10: Navigate to the following locations and look for the malicious components created by Scarab Bin ransomware like “HOW TO RECOVER ENCRYPTED FILES.txt” and make sure to delete them all.
- %APPDATA%
- %TEMP%
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step 11: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use [product-name] this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 12: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 13: Navigate to the listed paths below and look for the registry keys and sub-keys created by Scarab Bin ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 14: Delete the registry keys and sub-keys created by Scarab Bin ransomware.
Step 15: Close the Registry Editor and empty the contents of the Recycle Bin.
To ensure the removal of Scarab Bin ransomware from your system including the malicious components it has created on your system, follow the advanced steps below.
Perform a full system scan using [product-code]. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.
- After the scan is completed click the “Fix, Clean & Optimize Now”button.