What is .SEXY3 File Extension ransomware? And how does it carry out its attack?
.SEXY3 File Extension ransomware is a file-encrypting threat and a new variant of the notorious ransomware group known as GlobeImposter ransomware. Just like a typical ransomware infection, .SEXY3 File Extension ransomware aims to infect computers to encrypt important data and extort money from its victims.
The moment it infects a system, it will connect to its remote Command and Control server where it downloads more malicious files and drops them into the system. It also makes changes in the Windows Registry so it can run every time users boot their PCs. After that, it will look for the following file types and begin encrypting important data.
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip
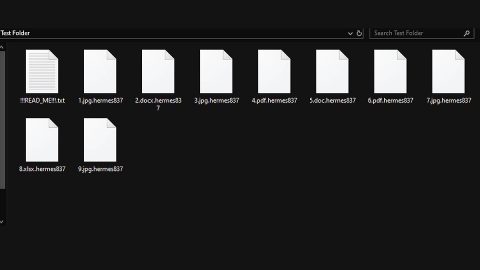
.SEXY3 File Extension ransomware uses a sophisticated encryption algorithm in encrypting files. After the encryption, it appends the .SEXY3 extension to each one of the encrypted files. It then opens an html file that contains the following ransom note:
“YOUR PERSONAL ID
ENGLISH
YOUR FILES ARE ENCRYPTED!
TO DECRYPT, FOLLOW THE INSTRUCTIONS BELOW.
To recover data you need decryptor.
To get the decryptor you should:
Send 1 crypted test image or text file or document to [email protected]
(Or alternate mail
[email protected])
In the letter include your personal ID (look at the beginning of this document).
We will give you the decrypted file and assign the price for decryption all files
After we send you instruction how to pay for decrypt and after payment you will receive a decryptor and
instructions We can decrypt one file in quality the evidence that we have the decoder.
MOST IMPORTANT!!!
Do not contact other services that promise to decrypt your files, this is fraud on their part! They will buy
a decoder from us, and you will pay more for his services. No one, except
[email protected], will decrypt your files.
Only [email protected] can decrypt your files
Do not trust anyone besides
[email protected]
Antivirus programs can delete this document and you can not contact us later.
Attempts to self-decrypting files will result in the loss of your data
Decoders other users are not compatible with your data, because of each user‘s unique encryption key”
How does .SEXY3 ransomware proliferate?
The same with other variants of GlobeImposter ransomware, .SEXY3 File Extension ransomware proliferates via spam emails containing malicious attachments. Usually, crooks disguise such emails to make them look like they were from legitimate and well-known companies to trick users into opening the email and downloading the attachment. The infected attachment may be a document with macro scripts used to launch the GlobeImposter ransomware variant into the system.
For the removal of .SEXY3 File Extension ransomware, follow the given steps below.
Step 1: Tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step 2: Go to Processes and look for the malicious process of .SEXY3 File Extension ransomware then right clicks on it and select End Process or End Task.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for dubious programs that might be related to .SEXY3 File Extension ransomware and then Uninstall it/them.

Step 5: Tap Win + E to launch File Explorer.
Step 6: From there, navigate to the following directories listed below and look for the malicious components of .SEXY3 File Extension ransomware and remove them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step 7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use [product-name], this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the listed paths below and look for the registry keys and sub-keys created by .SEXY3 File Extension ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 10: Delete the registry keys and sub-keys created by .SEXY3 File Extension ransomware.
Step 11: Close the Registry Editor.
Step 12: Empty your Recycle Bin.
Complete the removal process of .SEXY3 ransomware by using a trusted and reliable program like [product-name]. Refer to the following guidelines on how to use it.
Perform a full system scan using [product-code]. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.