What is Powermediatabsearch.com? And how does it work?
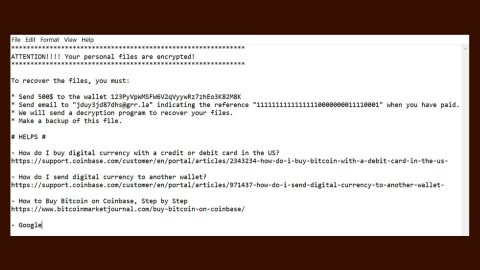
Powermediatabsearch.com is a browser hijacker that stealthily infiltrates your computer. It replaces your home page and search engine once it infects your computer. Although it does not directly damage your computer, this browser hijacker however, can be a way for other severe infections to get in your computer such as Trojans, ransomware, etc.
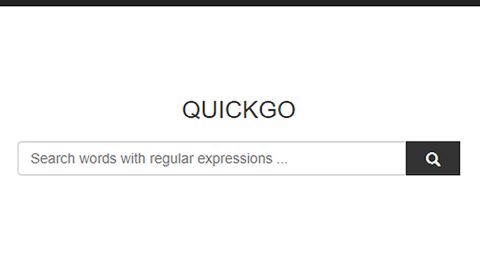
At first glance, Powermediatabsearch.com looks like a legitimate search engine that offers several features like quick links to social media pages, media services, gaming sites and more compared to other popular search providers. No wonder most users fell for its appearance, not knowing that this search engine can monitor their browsing activities to gather personal information. The information gathered is based on your browsing activities.
How is Powermediatabsearch.com distributed?
Powermediatabsearch.com spreads through repackaged software bundles along with other freeware or shareware programs. Even if the unwanted programs can be easily disclosed, most users don’t know how to do it or they just don’t bother doing it so they end up with an unwanted program in their computer.
The removal instructions below will help you remove Powermediatabsearch.com:
Google Chrome
- Tap Win + E to open File Explorer.
- Navigate to this path:%LocalAppData%\Google\Chrome\User Data\Default
- Remove Preferences, Secure Preferences and Web Data
- After that, empty the Recycle Bin.
Mozilla Firefox
- Tap Win + E to open File Explorer.
- Navigate to this path:
“%AppData%\Mozilla\Firefox\Profiles\{Unique Mozilla user ID}
- After that, open js with Notepad.
- Change the user_pref(“browser.startup.homepage”, “http://powermediatabsearch.com”) with your preferred web address.
The next step for Internet Explorer below is not recommended for you if you don’t know how to navigate the Registry Editor. Making registry changes can highly impact your computer. So it is highly advised to use PC Cleaner Pro instead to get rid of the entries that Search.searchquickm.com created. So if you are not familiar with the Windows Registry skip to the advanced steps onwards.

However, if you are well-versed in making registry adjustments, then you can proceed.
Internet Explorer
- Press Win + R to open Run.
- Type in regedit and click OK to open the Registry Editor.
- Change the value data of http://powermediatabsearch.com in the following registry keys:
- HKLM\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Main\Start Page (64-bit!)
- HKLM\SOFTWARE\Microsoft\Internet Explorer\Main\Start Page
- HKCU\Software\Microsoft\Internet Explorer\Main\Start Page
- Navigate to the following path and change the value names in HKCU\SOFTWARE\Microsoft\Internet Explorer\SearchScopes\{0633EE93-D776-472f-A0FF-E1416B8B2E3A}
- FaviconURL (value data: “http://powermediatabsearch.com/favicon.ico”)
- FaviconURLFallback (value data: “http://powermediatabsearch.com/favicon.ico”)
- TopResultURL (value data: “http://powermediatabsearch.com”)
- URL (value data: “http://powermediatabsearch.com”)
- Close the Registry Editor.
Follow the continued advanced steps below to ensure the removal of Powermediatabsearch.com:
Perform a full system scan using SpyRemover Pro.
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch SpyRemover Pro.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Pro to protect your computer from future threats.