What is MadBit ransomware? And how does it execute its attack?
MadBit ransomware is a file-encrypting malware first observed on December 29, 2017. Based on the analysis made by security researchers, this crypto-malware is actually an original program that features snippets of open-source code. MadBit ransomware is designed to generate a unique pair of encryption and decryption keys – one is used to encrypt the targeted files while the latter is used to restore the encrypted files. The decryption key is then stored in a remote server managed by the cybercriminals behind MadBit ransomware.
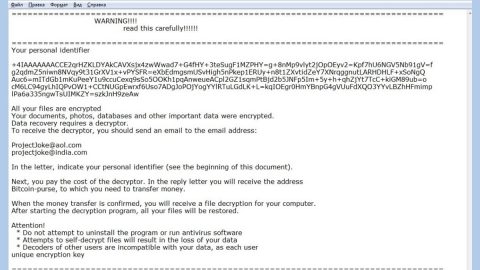
Before it starts encrypting the files, MadBit ransomware deletes the shadow volume copies of its targeted files, making it hard for its victims to recover them without the decryption key. During the encryption, this file-encrypting threat uses the AES encryption algorithm in encoding the files. It then adds the .enc extension after every file’s names to mark the encrypted files. After the encryption process, displays an alert which is shown in a message box labeled “madbit encryptor: Hello, you are encrypted!” containing the following text:
“***!WARNING!***
***YOUR COMPUTER ARE INFECTED***
***ALL DATABASES, SITES AND USERS HOME FILES HAVE BEEN ENCRYPTED***
================================================
>>>You have to pay for decryption in Bitcoins. The price depends on how fast you write to us.<<< ***After payment we will send you the decryption tool ,that will decrypt all your files.*** ===FREE DECRYPTION AS GUARANTEE=== ===Before paying you can send to us up to 1 files for free decryption=== Please note: that files must NOT contain valuable information and their total size must be less than 1Mb === Important information === YOUR COMPUTER UID : COPY&SEND YOUR UID TO EMAIL’S :
[email protected] ================================================ ***!WARNING!*** ===****rnadbit***madbit***madbit***madbit***madbit***madbit***madbit***madbit***madbit****===”
The ransom amount demanded the encrypted files’ decryption varies from the time period during which the victim manages to get in touch with the developers of MadBit ransomware who insist that victims should pay in Bitcoins to keep their anonymity. In addition, if you’re one of the unfortunate victims of MadBit, the crooks encourages you to send one file which must be less than 1MB to see if the decryptor really works. However, it’s obviously only a ploy to get you to pay the ransom. And besides security experts do not advise you to pay the ransom as you would only waste your money and time and that you might only be tricked to pay more than the original ransom amount.
For now, the best thing you could do is to eliminate MadBit ransomware before it causes further damage to your files and use any backup copies you have until security experts are able to develop free decryptor.
How does MadBit ransomware disseminate its malicious file(s)?
It seems that MadBit ransomware uses malicious spam email campaigns in disseminating its malicious files. That’s why you have to be cautious in opening emails even though it seems like they came from well-known companies as cyber crooks tend to pretend that the email is sent by some famous companies or groups to lure users in opening the email and the attachment. The attachment may be a macro-enabled document which contains scripts used to launch the attack on the infected computer.
Refer to the following instructions below to eliminate MadBit ransomware from your PC.
Step 1: Close the ransom note of MadBit ransomware and tap the Win + E keys to open File Explorer.
Step 2: Navigate to the following locations and look for the malicious files created by MadBit ransomware and delete all of them.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- %HOMEDRIVE%\user | ransom.jpg
- %USERPROFILE%\Desktop | READ_IT.txt
Step 3: Close the File Explorer and tap Ctrl + Shift + Esc keys to open the Task Manager.

Step 4: After opening the Task Manager, look for MadBit ransomware’s malicious process, right click on it and select End Process or End Task.

Step 5: Close the Task Manager.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 6: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 7: Navigate to the following path:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
Step 8: Look for any suspicious values created by MadBit ransomware and delete them.
Step 9: Close the Registry Editor and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 10: Look for MadBit ransomware or any suspicious program and then Uninstall it/them.

Step 11: Close Control Panel and empty your Recycle Bin.
Ensure the removal of MadBit ransomware from your computer as well as the malicious files it created with the help of the advanced removal instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. The installation will start automatically once a download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.