What is GottaCry ransomware? And how does it execute its attack?
GottaCry ransomware is a new cryptovirus discovered recently. This new ransomware threat does not encrypt files but deletes files that are located on the Desktop of an infected computer. It also displays a pop-up window that contains instructions on how to recover the deleted files.

Once it executes its attack, GottaCry ransomware will make modifications in some of the critical system files and settings in order to launch and repress system processes. It also employs the data gathering module to collect information about the system and its user. The harvested data, along with the malicious components of GottaCry ransomware are then used for the next module called stealth protection. This second module scans the system for any digital signature of security programs and prevents them from detecting GottaCry ransomware.
In addition, it also alters some registry keys and entries in the Windows Registry. As a result, it can run automatically on every startup and continue its attack. Following all these alterations, it will delete all the files that are located on the desktop and supposedly move them to a server. It also opens a program window labeled “GottaCry | Windows encryptor” which contains the following content:
“GottaCry Windows Decryptor 2019
Your computer has been encrypted
All your files were encrypted
If you turn off your computer, we will leak all your passwords and will delete your computer
All your desktop files were moved to my server until payment is done
All of your passwords were recovered into my servers.
Contact only on discord!
DISCORD: Russen#6061
50$ bitcoin or $70 PayPal
1HfdBrUDYZ1rCdQcgBt84Ja7JoYhHDqNcg”
Based on the ransom note, the files located on the desktop were supposedly moved to a server and will stay there until victims pay the ransom amount of $50 or $70. Moreover, according to the analysis done by security experts, the current samples related to GottaCry ransomware indicates that this threat does not really function as ransomware as it seeks to delete files instead of encrypting them. If you are one of the victims of this malware, the best thing you can do with the hand you are dealt with is to prioritize the removal of GottaCry ransomware before it can get rid of your other important files.
How is the payload file of GottaCry ransomware disseminated over the web?
The payload file of GottaCry ransomware could be disseminated using several distribution techniques but its creators mostly use malicious spam email campaigns. In these emails, cyber crooks attach an infected file. The infected file may be a PDF file, executable file, document with macro scripts used to launch the crypto-malware in the system. This is why it’s important to always practice precaution when downloading files, not just in emails but all over the internet.
Wipeout GottaCry ransomware from your computer with the help of the following removal instructions.
Step_1: Close the program window of GottaCry ransomware. If you find it hard to do so, you can close it via Task Manager. Just tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step_2: Next, go to the Processes tab and look for the malicious processes of GottaCry ransomware and then right-click on it and select End Process or End Task.
Step_3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in “appwiz.cpl” and then click OK or press Enter.
Step_4: Look for dubious programs that might be related to GottaCry ransomware and then Uninstall it/them.
Step_5: Close Control Panel and then tap Win + E to launch File Explorer.
Step_6: After opening File Explorer, navigate to the following directories below and look for GottaCry ransomware’s malicious components such as GottaCry.exe, [random].exe, and other suspicious-looking files and then erase them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step_7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step_8: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_9: Navigate to the listed paths below and look for the registry keys and sub-keys created by GottaCry ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_10: Delete the registry keys and sub-keys created by GottaCry ransomware.
Step_11: Close the Registry Editor.
Step_12: Empty your Recycle Bin.
Try to recover your encrypted files using their Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if GottaCry ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Congratulations, you have just removed GottaCry Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove GottaCry Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
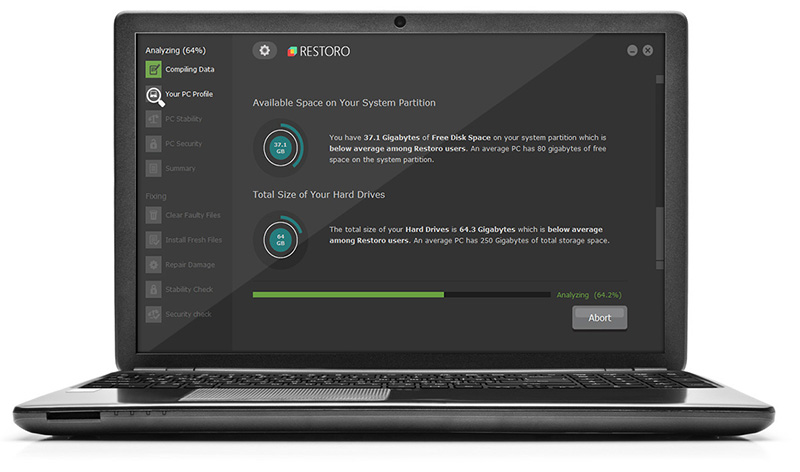
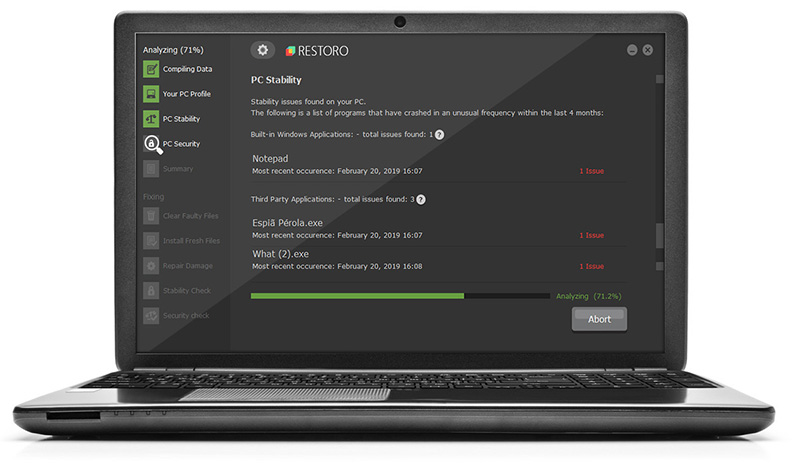
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.