What is Search.searchipdf2.com? And how does it function?
Search.searchipdf2.com is yet another suspicious browser extension developed by Polarity Technologies. It is also known as “PDF Convert” which allows users to convert PDF files to other formats. Aside from that, this suspicious browser extension supposedly functions as a search engine that claims to provide users with improved search results to enhance their browsing experience. It may look like your typical search provider but it’s not really what it looks like as it is actually categorized as a browser hijacker by security experts.
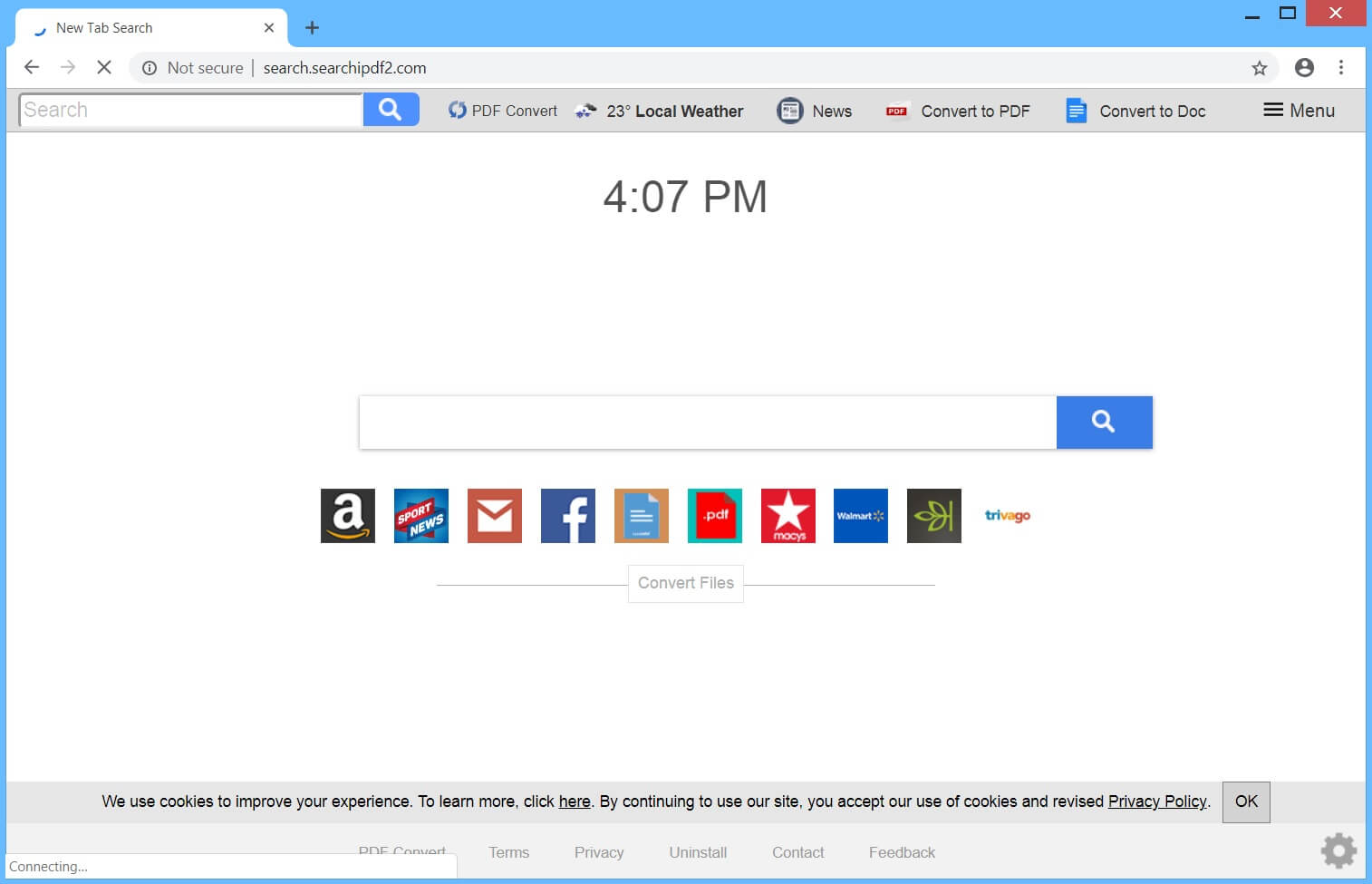
If it gets installed, Search.searchipdf2.com will alter the default settings in your browser such as the default search engine, homepage, and even the new tab page. It can also add other shady browser extensions, add-ons, toolbars, and many more. This allows the browser hijacker to manipulate your browsing and inject any websites you visit with tons of sponsored content from its affiliated sites. This browser hijacker also causes redirects to some unknown websites.
However, not all the sites it takes you to can be trusted for some of them might have harmful or malicious content. Moreover, Search.searchipdf2.com also keeps track of your every activity online in order to obtain browsing information like websites you visited, search queries, your ISP, browser type, OS version, and many more. The information obtained is used and processed so that it can display more ads that are to your liking. As you can see, nothing good can come out of using Search.searchipdf2.com so you have to remove it from your browser and computer as soon as you can.
How is Search.searchipdf2.com disseminated over the web?
Search.searchipdf2.com is disseminated over the web using several distribution techniques but its developers commonly used software bundling. In this method, Search.searchipdf2.com is added as one of the extra programs in software bundles that are offered on free sharing sites. If you don’t want pesky browser hijackers and other unwanted programs like Search.searchipdf2.com from infecting your browser and computer, it’s best if you use the recommended Advanced or Custom setup when installing software bundles as it allows you to get rid of any extra programs added in the package before you proceed with the installation.
Remove Search.searchipdf2.com from your browser and your computer by using the instructions given below as a reference.
Step_1: You have to flush the DNS cache of your computer first. To do so, right-click on the Start button and click on Command Prompt (administrator). From there, type the “ipconfig /flushdns” command and tap Enter to flush the DNS.
Step_2: After that, restart your computer and then open all the browsers infected by Search.searchipdf2.com. Reset all the affected browsers to default to their default state.
Google Chrome
- Open Google Chrome, then tap the Alt + F keys.
- After that, click on Settings.
- Next, scroll down until you see the Advanced option, once you see it, click on it.
- After clicking the Advanced option, go to the “Restore and clean up option and click on the “Restore settings to their original defaults” option to reset Google Chrome.
- Now restart Google Chrome.
Mozilla Firefox
- Open Mozilla Firefox and tap Ctrl + Shift + A to access the Add-ons Manager.
- In the Extensions menu Remove the unwanted extension.
- Restart the browser and tap keys Alt + T.
- Select Options and then move to the General menu.
- Overwrite the URL in the Home Page section and then restart the browser.
Internet Explorer
- Launch Internet Explorer.
- Next, click the wrench icon for Settings.
- Then click Internet Options.
- After that, go to the Advanced tab.
- From there, click the Reset button. This will reset Internet Explorer’s settings to their default condition.
- Now click OK to save the changes made.
- Restart your computer.
Step_3: Next, tap the Win + R keys to open the Run dialog box and type “appwiz.cpl” in the field and press Enter to open the Programs and Features in Control Panel.
Step_4: From the list of programs installed, look for Search.searchipdf2.com or any unfamiliar program that could be related to it under the list of installed programs, and once you’ve found it, uninstall it.
Step_5: Edit your Hosts File.
- Tap the Win + R keys to open then type in %WinDir% and then click OK.
- Go to System32/drivers/etc.
- Open the hosts file using Notepad.
- Delete all the entries that contain Search.searchipdf2.com.
- After that, save the changes you’ve made and close the file.
Step_6: Hold down Windows + E keys simultaneously to open File Explorer.
Step_7: Navigate to the following directories and look for suspicious files associated with the browser hijacker such as the software bundle it came with and delete it/them.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %TEMP%
Step_8: Close the File Explorer.
Step_9: Empty the contents of Recycle Bin.
Congratulations, you have just removed Search.searchipdf2.com Hijacker in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
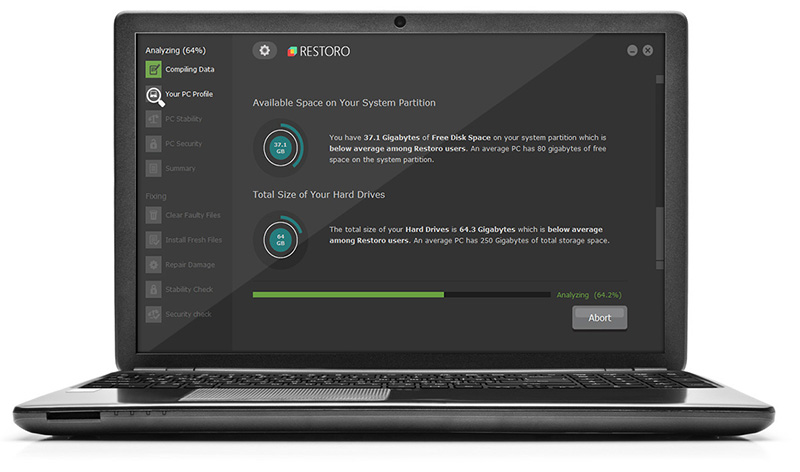
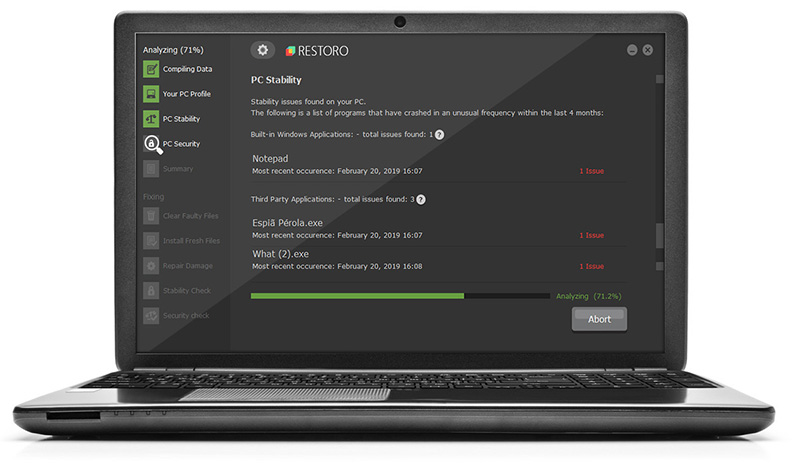
Now that’s how you remove Search.searchipdf2.com Hijacker in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.