What is LockCrypt ransomware? And how does it implement its attack?
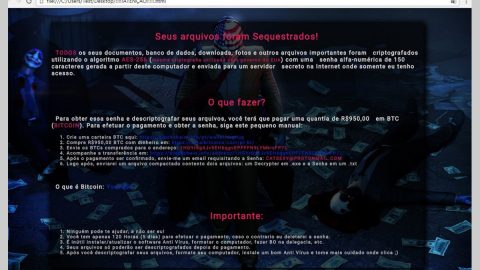
LockCrypt ransomware is a new ransomware Trojan that is being actively distributed over hacked remote desktop services. This new ransomware variant was detected in the last week of February 2018. When installed, LockCrypt ransomware implements its attack by scanning the computer for files to encrypt. Once it founds the files, it will begin its encryption process using the base64 encryption strategy and append the .1btc extension to the encrypted file names. Following data encryption, it drops its ransom note in a file named Restore Files.txt that provides detailed information of what has happened to the victim’s files. Here’s the full content of the ransom note:
“Your ID xxx
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail support: [email protected] or [email protected]
Write this ID in the title of your message
In case of no answer in 24 hours write us to these e-email support: [email protected] or [email protected]
You have to pay for decryption of Bitcoins. The price depends on how fast you write to us. After payment, we will send you the decryption tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 3 files for free decryption. The total size of files must be less than 10Mb(nonarchived), and files should not contain valuable information.
(databases, backups, large excel sheets, etc.)
How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site.You have to register, click ‘Buy bitcoins’, and select the seller payment method and price.
https://localbitcoins.com/buy_bitcoins
Also, you can find other places to buy Bitcoins and beginners guide here:
http://www.coindesk.com/information/how-can-i-buy-bitcoins/
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.”
As you can see, the cyber crooks did not mention how much then ransom is but they did mention that the ransom will depend on how fast the victim manages to contact them right after the attack. Note that this is merely a tactic to get its victims to reach out to them right away so that they can demand a big ransom and this is something you must not do. Not only is it a waste of time but you might also end up losing a big amount of money for nothing. Unfortunately, there is no free decryptor available yet to decrypt the encrypted files of LockCrypt ransomware. But you can use whatever backup copy you have of the affected files on your computer.
How does LockCrypt ransomware spread its malicious payload?
AS pointed out early on, this new version of LockCrypt ransomware spreads through remote desktop services where developers of this ransomware login to the targeted computer and install the ransomware themselves. To prevent this kind of attack, where hackers login to a computer and execute the ransomware, it is recommended to lock the service correctly and that the PC running remote desktops services should be placed behind VPNs to block any kind of unauthorized access of those who don’t have VPN accounts connected to your network.
Use the following removal instructions to obliterate LockCrypt ransomware from your infected system effectively.
Step 1: Open the Windows Task Manager by pressing Ctrl + Shift + Esc at the same time. Proceed to the Processes tab and look for suspicious processes that can be related to LockCrypt Ransomware.

Right-click on the processes then click Open File Location and scan them using a powerful and trusted antivirus like SpyRemover Pro. After opening their folders, end their processes and delete their folders. If the virus scanner fails to detect something that you know is suspicious, don’t hesitate to delete it.
Step 2: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK.

Step 3: Look for LockCrypt ransomware or any malicious program and then Uninstall it.

Step 4: Hold down Windows + E keys simultaneously to open File Explorer.
Step 5: Go to the directories listed below and then look for the malicious files used in installing LockCrypt ransomware into your computer as well as the files the ransomware has created during its attack and remove them all.
- C:\Users\(your pcname)\AppData\Roaming
- %TEMP%.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step 6: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 7: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 8: Navigate to the following path:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 9: Delete the registry keys and sub-keys created by LockCrypt ransomware.
Step 10: Close the Registry Editor and empty your Recycle Bin.
It is important to make sure that nothing is left behind and that LockCrypt ransomware is completely removed use the following antivirus program. To use it, refer to the instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. The installation will start automatically once a download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.

Register the program to protect your computer from future threats.