What is Scarab Turkish ransomware? And how does it implement its attack?
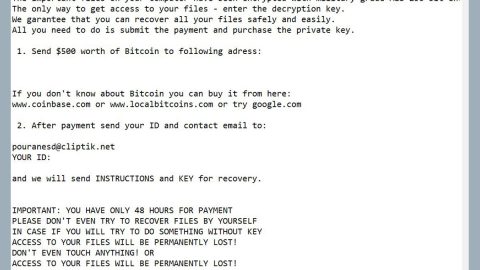
Scarab Turkish ransomware is one of the latest variants of the infamous Scarab ransomware. This new variant seems to target Turkish users and like other Scarab variants, it still follows the same behaviors when it comes to implementing its attack. It starts by employing a data gathering module used to obtain information about the infected computer and its user. The gathered data is classified into two which is personal data and campaign metrics. The harvested data is then used by another module called stealth protection which can scan the system for any security measures that could interfere with its attack. After that, it alters some registry entries and sub-keys which allows it to run automatically in every system boot. Once all these modifications are successfully implemented, Scarab Turkish ransomware begins the encryption using a sophisticated encryption algorithm. Once it’s done, it releases a ransom note written in Turkish language stating:
“SISTEMINIZDEKI DEGER GORULEN VERILERIN TUMU TARAFIMCA SIFRELENMISTIR.
VERILERINIZI GERI ALMAK ICIN ASAGIDA SIZE YAZDIGIM MAIL ADRESINDEN BANA ULASABILIRSINIZ.
BANA MAIL ADRESINIZDE IP ADRESINIZI GONDERMEYI UNUTMAYIN.
[email protected]
BUNUN YANINDA;
GENELDE SERVERINA GIRDIGIMIZ MUSTERILERIN TEREDDUTLERI ODEME YAPTIKTAN SONRA DOSYALARIMIZ GELMESSE KOMSUMUZ HACKLENDI DOSYALARI ACILMADI
EKSIK ACILDI VS. VS. VS. MALESEF SON ZAMANLARDA BU YAPTIGIMIZ ISIN TRENDLESMESI SONUCU BU TARZ SEREFSIZLIKLER YAPAN VAR PEKI BANA NASIL GUVENECEKSINIZ
SU SEKILDE BELIRTEYIM DAHA ONCE HACKLEDIGIM BIR FIRMAYI REFERANS AMACLI SOYLEYEBILIRIM ARAR SORARSINIZ
BIR DIGER KONUYA GELIRSEK
YAPTIGIMIZ SIFRELEMEYI BIZDEN BASKA ACABILEN YOK SAGA SOLA GONDERIYORSUNUZ SERVERLARI ADAMLAR SIZDEN ALACAGIMIZ RAKAMINDA USTUNE RAKAM EKLEYEREK
KENDILERI SIFRELERI COZMUS GIBI ISINIZI GORUYORLAR BIRCOK VERI KURTARMA FIRMASIYLADA CALISYORUZ, CALISYORUZ DERKEN ORTAKLIK VS. DEGIL SIZIN ONLARA GONDERDIGINIZ
SERVERLARIN SIFRELERINI SIZE DEGIL AYNI RAKAMA ONLARA VERIYORUZ ONLARDA KARLARINI EKLEYEREK SIZE VERI KURTARMA HIZMETINI VERMIS OLUYOR
BIR DIGER KONU LUTFEN SAAT 10:00’A KADAR DONMUS OLUN BUNUN NEDENLERINE GELIRSEK
GERCEKTEN COK YOGUN BIR TEMPO ILE CALISYORUZ BIZIM ICIN VAKIT SIZIN YAPACAGINIZ ODEMEDENDE ONEMLI BIR SONRAKI GUNUN SERVERLARININ HAZIRLANMASI SIFRELENMESI
BIZDE NETICEDE INSANIZ UYKU YEMEK SOSYAL AKTIVITELER DERKEN VAKTIMIZ KALMIYOR ELIMIZDE ONLARCA IS VARKEN GERIYE DONUP 1 ISLE UGRASAMIYORUZ SIFRELEDIGIMIZ VERILERIN
SIFRELERI 1234 KOYACAK KADAR AMATOR DEGILIZ YADA DATALARI TURKISH PROGRAMLARI, SHADOW EXPLORER ILE KURTARACAGINIZ BIR SEKILDE BIRAKMIYORUZ YANI OYALANMANIN SAGA SOLA
SORMANIN BIR MANASI YOK VAKITLICE DONUN HERKES VAKITLICE ISINI YAPSIN
BIR DIGER KONU SAVCILIGA GIDECEK ARKADASLAR ICIN BU KISIM
BANKA HESAP NUMARASI ISTEYIP DURMAYN CUNKU BANKA HESABI KULLANMIYOR”
How does Scarab Turkish ransomware proliferate?
Like other Scarab variants, this one proliferates using spam emails where crooks attach an obfuscated file. This obfuscated file may be a ZIP file, a PDF file or a document with macro scripts used to launch Scarab Turkish ransomware in the targeted computer. Thus, you need to pay extra attention and make sure to always double check an email before you download its attachment as it might be a malicious payload of dangerous threats like Scarab Turkish ransomware.
Kill Scarab Turkish ransomware by following the removal guide prepared below.
Step 1: Tap the Ctrl + Alt + Delete keys to open a menu and then expand the Shutdown option which is right next to the power button.
Step 2: After that, tap and hold the Shift key and then click on Restart.
Step 3: And in the Troubleshoot menu that opens, click on the Advanced options and then go to the Startup settings.
Step 4: Click on Restart and tap F4 to select Safe Mode or tap F5 to select Safe Mode with Networking.
Step 5: After your PC has successfully rebooted, tap Ctrl + Shift + Esc to open the Task Manager.

Step 6: Go to the Processes tab and look for any suspicious-looking processes that could be related to Scarab Turkish ransomware and then end their processes.

Step 7: Exit the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 8: Look for suspicious programs that could be related to Scarab Turkish ransomware and then uninstall them.

Step 9: Close Control Panel and tap Win + E keys to open File Explorer.
Step 10: Navigate to the following locations and look for the malicious components created by Scarab Turkish ransomware like [random].exe and make sure to delete them all.
- %APPDATA%
- %TEMP%
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step 11: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use [product-name] this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 12: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 13: Navigate to the listed paths below and look for the registry keys and sub-keys created by Scarab Turkish ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 14: Delete the registry keys and sub-keys created by Scarab Turkish ransomware.
Step 15: Close the Registry Editor and empty the contents of the Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if Scarab Turkish ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

To ensure the removal of Scarab Turkish ransomware from your system including the malicious components it has created on your system, follow the advanced steps below.
Perform a full system scan using [product-code]. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.
- After the scan is completed click the “Fix, Clean & Optimize Now”button.