Researchers have been monitoring Spectre Ransomware for awhile now. Spectre Ransomware is a ransomware Trojan that was observed in June 9, 2017 which was still in testing mode that time but a few days later, a full version was released. Spectre Ransomware is a new malicious program that has been spreading all over the web lately. This ransomware Trojan is considered to be a sophisticated one since a considerable amount of time and resources have been accumulated to create this threat. For that reason, researchers consider Spectre Ransomware and its variants to be a great threat to computer users.

The Spectre Ransomware carries out a typical encryption process. it is designed to connect to its Command and Control Server or C&C a0142503.xsph.ru/testing.php?mode=a1 as it enters your computer. The C&C server responds with your unique ID and then proceeds to encrypt your files. It scans your computer for files especially the important ones such as the files that you recently opened or modified and then starts the encryption process using a powerful AES-256 cipher algorithm. In the encryption process, the Spectre Ransomware appends the .spectre file extension at the end of the file’s name. The ransomware Trojan currently targets 21 different files with the following extensions:
.txt, .doc, .docx, .pdf, .rtf, .xls, .xlsx, .ppt, .pptx, .bmp, .jpg, .jpeg, .gif, .tiff, .png, .wav, .mpeg, .avi, .zip, .rar, .wmv.
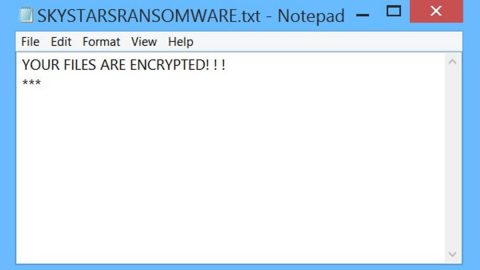
Once all of these files are encrypted, the ransomware Trojan communicates to the C&C server about the number of encrypted files and then proceeds to drop you the rasom note through a HowToDecryptIMPORTANT!.txt file containing the following message:
“IMPORTANT INFORMATION!
All your files are encrypted by encryption algorithm AES-256, you can’t decrypt your files without a key.
If you want to decrypt your files you should pay 200$.
To decrypt your files go to http://a0142503.xsph.ru/login.php your ID:”
Based on the ransom note, you have to go to the link to decrypt your files. And once you open it, a tab with Spectre will be displayed. The site greets you with a message saying that “Your documents, photos, databases and other important files have been encrypted!” and demands you to buy the decryptor program for $200. This site also provides you FAQ, Support and Decryptor pages that has information about encryption decryption and ransom payment. One thing you should never consider is paying the ransom. The main goal of most ransomware is to swindle money from you and once you give in to their demands, the recovery of your files becomes only a matter of their conscience. So it goes without saying that getting rid of this ransomware Trojan from your computer is your topmost priority to prevent it from infecting all of your files.
Removing Spectre Ransomware:
- Kill the malicious process by pressing Alt + F4.
Locate the Spectre Ransomware or any suspicious processes. Right-click on them and select Open File Location then scan them using any up-to-date antivirus. After opening each folder, end the infected processes and delete their folders.
- Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK.


Locate any suspicious program that might be related to Spectre Ransomware and then Uninstall it.
5. Open System Configuration by clicking the Windows button and typing msconfig in the search box. Go to Startup and unmark items with an unknown manufacturer.
6. Delete everything under these directories.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %TEMP%
- %APPDATA%
Erase everything on the Temp folder.
- Empty the Recycle bin.
- Scan your computer using SpyRemover Pro to make sure that your computer is safe from the Spectre Ransomware and to ensure that all its leftover have been removed from your computer as well. It would really be a big help to have this kind of antivirus and anti malware from your computer to prevent ransomware like Spectre and other threats for that matter from infecting your computer in the future.
Restoring your encrypted files:
You can restore the encrypted files without resorting to paying the ransom with the help of Window Previous Versions feature. Keep in mind that this method is only effective if the System Restore function was enabled in your computer’s operating system and that using this method of file recovery may not work for everyone because some variants of the Spectre Ransomware removes the shadow volume copies of the files. Nevertheless, it is still very much worth the try one of the best methods available.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.