What is aZaZeL ransomware? And how does it work?
aZaZeL ransomware is a file encrypting threat that holds its victims’ files hostage in exchange for a ransom. It hijacks the system by dropping an executable file to the targeted computer. This executable file is typically obfuscated and may look like a legitimate system process or application to trick users into running it. If you open the executable file, the rest of the ransomware’s components establish its connection with the command and control server or C&C server. Once this happens, your computer will be controlled by the cyber criminals behind the aZaZeL ransomware. It executes a command to download the latest updates of the ransomware’s codes to the system. The updates will implement improvement to the ransomware’s functionalities and make some adjustments on your computer to make is removal difficult.
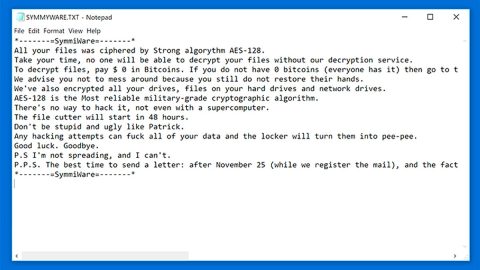
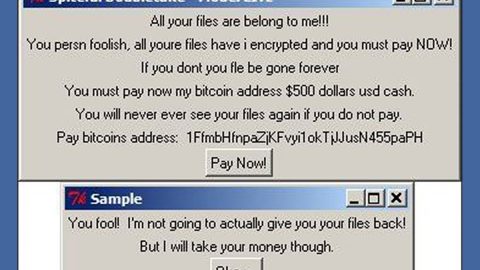
Moreover, the aZaZeL ransomware starts to scan the infected computer for targeted files and then appends the .Encrypted file extension, using the AES algorithm, that is used to mark the locked files. It then creates another file named, File_Encryption_Notice.txt that is usually dropped on your desktop and contains more information about the recovery procedure of the encrypted files. It also contains information like an email address, [email protected], which should be used to reach out to the crooks behind aZaZeL ransomware. Although this ransomware only requires a small amount of ransom money, that should not put your mind at ease and pay the ransom. Why? Paying the ransom is not an assurance that you’ll get your files back. It might be another ploy to deceive you and extort more money from you, so paying the ransom, no matter how small the amount is, is not advised.
How is aZaZeL ransomware distributed?
There are several ways that this ransomware can get into your computer. The common distribution methods are through drive-by downloads, malware infected software updates and malicious spam email attachments. All of these are usually in the guise, be it an email attachment or software update that uses the names of famous companies that often deceives users most of the time. So if you find yourself at the mercy of this ransomware, do not be desperate enough to pay the ransom and look for alternative solutions to remove the ransomware instead.
Follow the removal guide below to get rid of aZaZeL ransomware:
Step 1: Open Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.
Step 2: Go to the Processes tab and look for any suspicious processes and then kill them.
Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for aZaZeL Ransomware or any suspicious program and then Uninstall.

Step 5: Hold down Windows + E keys simultaneously to open File Explorer.
Step 6: Go to the directories listed below and delete everything in it. Or other directories you might have saved the file related to aZaZeL Ransomware.
-
%USERPROFILE%\Downloads
-
%USERPROFILE%\Desktop
-
%TEMP%
Step 7: Look for the following malicious executable file that might be related to aZaZeL ransomware.
Step 8: Right-click on it and click Delete.
Step 9: Empty the Recycle Bin.
Step 10: Try to recover your encrypted files.
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if the aZaZeL Ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Follow the continued advanced steps below to ensure the removal of the aZaZeL Ransomware:
Perform a full system scan using SpyRemover Pro.
-
Turn on your computer. If it’s already on, you have to reboot it.
-
After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
-
To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit Enter.
-
Windows will now load the Safe Mode with Networking.
-
If done correctly, the Windows Run Box will show up.
-
Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
-
A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
-
Click OK to launch SpyRemover Pro.
-
Run SpyRemover Pro and perform a full system scan.
-
Register SpyRemover Pro to protect your computer from future threats.