What is Blocking ransomware?
Blocking ransomware is a new variant of the BTCWare ransomware family which has been active since April 2017. Blocking ransomware emerged on the first week of August 2017 and seems to have the same source code as other BTCWare variants, making it as dangerous as can be. Aside from the similarities in the source code of the malware, this ransomware also carries out typical ransomware attack; encrypts your important files using a strong encryption algorithm and marks the targeted files by modifying their file extensions.
How does this ransomware function?
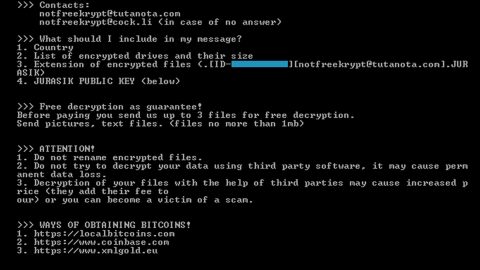
Once it had successfully infiltrated your computer, it’ll start to scan your computer for files to encrypt. After that, it encrypts those files with [[email protected]].blocking extensions. The [email protected] serves as an indication to contact the crooks behind the malware. Right after the encryption, the virus drops a ransom note containing the documents Info.hta and !#_READ_ME_#!.hta. Here’s the full context of the ransom note:
“All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail [email protected] in body of your message write your ID
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the decryption tool that will decrypt all your files.
[FREE DECRYPTION AS GUARANTEE]
Before paying you can send to us up to 3 files for free decryption.
Please note that files must NOT contain valuable information
and their total size must be less than 1Mb
[HOW TO OBTAIN BITCOINS]
The easiest way to buy bitcoin is LocalBitcoins site.
You have to register, click Buy bitcoins and select the seller
by payment method and price
https://localbitcoins.com/buy_bitcoins
[ATTENTION]
Do not rename encrypted files
Do not try to decrypt your data using third party software, it may cause permanent data loss
If you not write on e-mail in 36 hours – your key has been deleted and you cant decrypt your files
Your ID:
[172 RANDOM CHARACTERS]”
As you can see, the developers of this ransomware seem serious since they do not hesitate to create a lengthy and detailed ransom note that explains how to recover the encrypted files. They then laid down the conditions of test decryption as a guarantee, promising you the recovery of your files once you pay the ransom. However, paying the ransom is not recommended, not to mention a dumb move for it does not guarantee that the crooks will hold their end of the bargain once they got the money. The best thing you can do is to look for other ways to get rid of the malware and recover your files which are thankfully provided on the last part of this article.
How does Blocking ransomware proliferate?
Just like other variants of the BTCWare ransomware, Blocking ransomware is mainly distributed through malicious spam email campaigns, exploit kits, fake software update downloads and other random suspicious links you may come across while browsing shady websites. To prevent the likes of this malware from infecting your computer you need to:
- Keep your system updated all the time by installing software updates only from reliable source.
- Avoid opening much less downloading suspicious email attachments especially if it came from unknown senders.
- Always keep your antivirus program up-to-date and run frequent system scans.
To eliminate Blocking ransomware, make sure to thoroughly follow each steps below as well as the following advanced steps.
Step 1: Open Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.

Step 2: Go to the Processes tab and look for any suspicious processes and then kill them.

Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 4: Look for Blocking Ransomware or any suspicious program and then Uninstall.

Step 5: Hold down Windows + E keys simultaneously to open File Explorer.
Step 6: Go to the directories listed below and delete everything in it. Or other directories you might have saved the file related to Blocking Ransomware.
- %HOMEDRIVE%\user
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %TEMP%
Step 7: Look for Rand123 folder and delete it.
Step 8: After that, locate other malicious files such as Blocking -Decrypter.exe created by Blocking ransomware and remove them as well.
Step 9: Empty the Recycle Bin.
Step 10: Try to recover your encrypted files.
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if the malware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Follow the continued advanced steps below to ensure the removal of the Blocking Ransomware:
Perform a full system scan using SpyRemover Pro.
- Turn on your computer. If it’s already on, you have to reboot it.
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit Enter.
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK. - A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch SpyRemover Pro.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Pro to protect your computer from future threats.