What is searchbee.net?
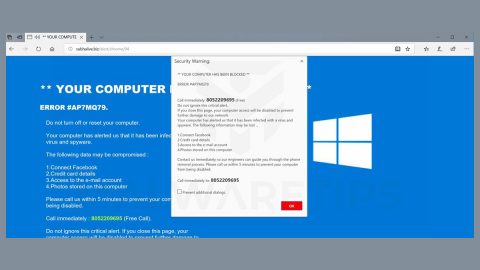
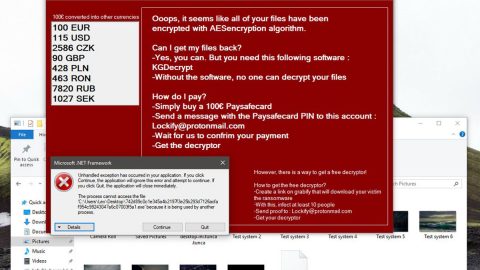
Claimed by the developers, searchbee.net is a “high-quality” Internet search engine that generates enhanced results and, therefore, and much improved the browsing experience. Upon first inspection, searchbee.net may seem legitimate and a useful tool, but, this website is promoted by rogue download/installation set-ups that immediately hijack browser options and stealthily alters various settings. In addition, searchbee.net tracks and records Internet browsing activity by collecting user-system information.

After its infiltration, the rogue set-ups hijack the commonly used internet browsers such as Internet Explorer, Google Chrome, and Mozilla Firefox, stealthily modifying the new tab URL, homepage, and default search engine options by assigning them to searchbee.net. Moreover, they append this URL to the target of each browser shortcut. Set-ups install a number of third party applications and/or browser extensions or simply called “helper objects” which automatically reassign the aforementioned settings when attempts are made to revert them back. Therefore, users are unable to return browsers to their previous states and continually encounter the annoying unwanted redirects to searchbee.net, which also significantly diminish the web browsing experience. Furthermore, browsing activity is continually tracked, since searchbee.net and helper objects continually record user-system information that might be personally identifiable such as the IP addresses, URLs visited, search queries, etc. and is later shared with or sold to third parties who misuse personal details to generate revenue. Definitely, the information tracking can lead to serious privacy issues and or even identity theft. If you encounter pesky unwanted redirects to searchbee.net, immediately eliminate all suspicious applications/browser plug-ins and never visit this rogue site again.
The searchbee.net hijacker is similar to the secure-surf.net, powerofsearches.com, speedydialsearch.com, and many other sites. As with searchbee.net, these sites also claim to improve the browsing experience, however, fake search engines are designed only to generate revenue for the developers’ benefit mainly. Rather than providing any significant value for regular users, instead, they cause unwanted redirects and continually record user-system information earn even more. Some even generate results leading to malicious and infectious websites. Moreover, using fake search engines can also lead to high-risk adware or malware infections.
How can searchbee.net install get in to the computer?
Primarily, this website is promoted through rogue downloaders/installers. And they are using this deceptive marketing method is called “bundling”. Users usually rush the download/installation processes and carelessly skip some steps and the developers are aware of this, so, they hide browser modifications details within the “Custom” or “Advanced” options of these processes. So by skipping this section, users may inadvertently grant set-ups permission to alter browser options, expose their systems to risk of various infections, and compromise their privacy.
How to avoid installation of potentially unwanted applications?
In order to prevent this situation, always be very cautious when downloading and installing software into your computer. First, always remember to select the “Custom/Advanced” settings and closely analyze each step. Second, always decline offers to download/install additional applications and opt-out of those already included. Take note to always be cautious to avoid such infection.
These instructions indicate how to get rid of Searchbee.net automatically. The instructions need to be applied on the infected computer.
- Turn the infected computer on. If it is turned on, restart it.
- When BIOS screen disappears after the reboot, tap F8 key repeatedly. Advanced Options menu will show up. If Windows logo appears, reboot the PC and try pressing F8 again.
- When you access Advanced Options menu, use arrow keys to navigate and choose Safe Mode with Networking. Press Enter to access the mode.

4.Wait for Windows to load Safe Mode with Networking.
5. Press and hold the Windows key and then press R key.


6. If you have pressed both keys correctly, Windows Run Box will pop up.
7. Type the following into the Open box:
explorer https://www.fixmypcfree.com/removal
- Note, that there has to be a single space gap in between iexplore and http. Click OK.
8. Internet Explorer will open and a download dialog bar will appear at the bottom of your screen. Click Run to begin the installation automatically once SpyHunter is downloaded.

9. Click OK if your system asks whether you want to run SpyRemover Pro software.
10. Run SpyRemover Pro and perform a full system scan.
11. Once all the malicious infections are detected, click Fix Threats. SpyRemover Pro will as you to register the software.
12. By registering SpyRemover Pro you will also be able to protect your computer from other potential threats. Once you have registered the program, the malware will be removed. Reboot your PC to fully implement the malware removal procedure.
Use an anti-malware program
We recommend using SpyRemover Pro, a highly effective and widely used malware removal program to clean your computer of Solimba Installer. In addition to Solimba Installer, this program can detect and remove the latest variants of other malware.
SpyRemover Pro has an intuitive user interface that is easy to use. To get rid of Solimba Installer, the first step is to install it, scan your computer, and remove the threat.
To remove Solimba Installer from your computer using SpyRemover Pro, you need to perform the following steps:
Basic steps of SpyRemover Pro:
Step 1. Run SpyRemover Pro installer
Click on the .exe file that just downloaded in the lower right corner of your browser window.
Step 2. Click Yes
Click Yes to accept the User Account Control settings dialog.
Step 3. Foll0w setup instructions
Follow the instructions to get SpyRemover Pro set up on your computer and you will be good to go!
“use a one click solution like SpyRemover Pro”
Why is automatic removal more recommendable?
- You know only one virus name: “SEARCH.SEARCHFASTLM.COM”, but the truth is you have infected by a bunch of viruses.
The SpyRemover Pro program detects this threat and all others. - SpyRemover Pro is quite fast! You need only few minutes to check your PC.
- SpyRemover Pro uses the special features to remove hard in removal viruses. If you remove a virus manually, it can prevent deleting using a self-protecting module, it takes hours and may damage your PC. If you even delete the virus, it may recreate himself by a stealthy module which you don’t want.
- SpyRemover Pro is compatible with any antivirus.
- SpyRemover Pro is convenient to use.