What is Battlefield ransomware? And how does it work?
Battlefield is a file-encrypting Trojan virus developed using the open source platform, HiddenTear. It utilizes the AES 256 encryption algorithm during its encryption attack and appends the .locked extension on the targeted files in your computer. After the encryption, it changes the wallpaper on your desktop with an image saying, “Oops! Your files have been encrypted!.” This tactic is also used by the notorious WannaCry ransomware after its attack.
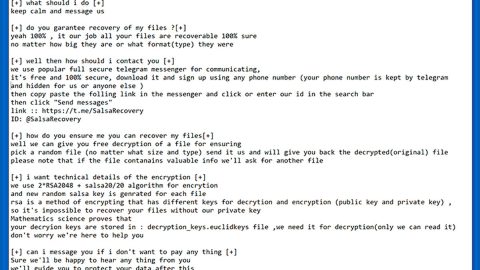
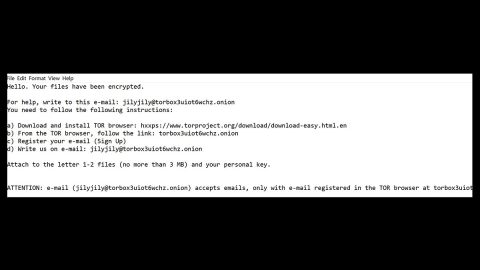
It then drops its ransom note in the form of a text file, named READ_ME.txt wherein the cyber criminals tells you that your files are encrypted by the Battlefield ransomware and that it can only be restored using a specific decryption tool. Here’s the full context of the ransom note:
“Ooops! Your files have been encrypted.
Warning: Never change the file names and extensions and their location.
Send the transaction code and user name of the system and the date and time of the Ransomware to the following email.
You must send 50 USD to this address.
Decrypt your files after payment!
Buy Bitcoin with Credit Card and send to me: [xxx]
Address Mail:[email protected]
BTC Address: [xxx]”
Even though the crooks demand only a small amount of money, paying them won’t do you any good. Not only you’ll risk your confidential information when you pay these crooks but it won’t guarantee you the recovery of your files since most victims of this kind of infection are often given the cold shoulder by the cyber criminals after they received the payment.
During its infiltration, this ransomware installs a malicious program named Battlefield-Decrypter.exe which is supposed to decrypt the encrypted files once you pay the ransom. However, there is no certainty that this decryption tool works, so it’s basically useless. And besides you can remove and recover your files using the instructions we have provided below.
How does Battlefield ransomware spread?
Usually, infections like Battlefield ransomware gets into your computer when you click or open or download a malicious link or file. It may be an email attachment, link, an ad, or a macro-enabled document file. Learning how threats like this spreads is very much essential in order to avoid getting infected by these threats. Thus, the common ways in which the crooks distribute their infections are:
- Malvertising
- Malicious spam email campaigns
- Fake software and fake software updates
- Exploit kits
- And as mentioned, macro-enabled documents
Mostly, cyber crooks makes use of obfuscated email attachments that may be disguised as something that would catch your attention to trick you into opening and downloading the infectious attachment.
Terminate the Battlefield ransomware using the complete set of instructions below in order to continue using your computer safely. Keep in mind that ransomware often spreads in a bundle with other types of malicious infection.
Step 1: Open Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.

Step 2: Go to the Processes tab and look for any suspicious processes and then kill them.

Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 4: Look for Battlefield Ransomware or any suspicious program and then Uninstall.

Step 5: Hold down Windows + E keys simultaneously to open File Explorer.
Step 6: Go to the directories listed below and delete everything in it. Or other directories you might have saved the file related to Battlefield Ransomware.
- %HOMEDRIVE%\user
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %TEMP%
Step 7: Look for Rand123 folder and delete it.
Step 8: After that, locate other malicious files such as Battlefield-Decrypter.exe created by Battlefield ransomware and remove them as well.
Step 9: Empty the Recycle Bin.
Step 10: Try to recover your encrypted files.
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if the malware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Follow the continued advanced steps below to ensure the removal of the Battlefield Ransomware:
Perform a full system scan using SpyRemover Pro.
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch SpyRemover Pro.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Pro to protect your computer from future threats.