What is AAC ransomware?
If you suddenly find your files inaccessible with a .aac extension, then it is clear you’re your computer has been infected with the AAC ransomware. AAC ransomware is another crypto-malware designed to encrypt files to make them unreadable. AAC ransomware seems to be connected with Xrat/Xorist ransomware family and it’s possible that one is based on the other. This ransomware was discovered in the last week of August 2017 and has been active since.
How does AAC ransomware execute its attack?
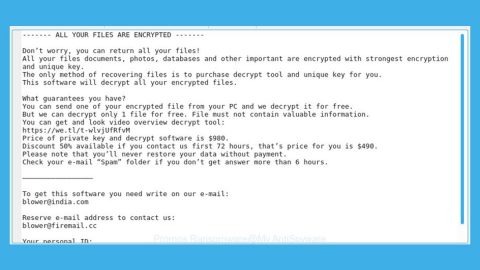
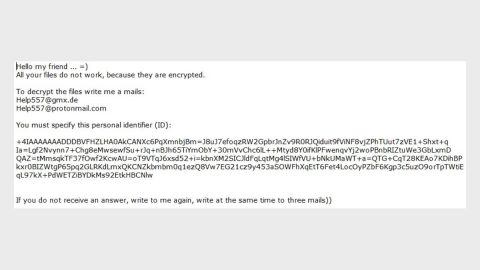
AAC ransomware uses Macro enabled documents that are spread out using spam emails. Once you open one, if the Macro function is enabled in your computer, the malware begins its attack by running the command in the document to install the AAC ransomware in the computer. After that, it scans all the directories on your computer to look for important files to encrypt. These files include audio, video, photos, databases, spreadsheets, texts, etc. The ransomware then communicates with its Command and Control server to receive and relay information about the compromised computer. During the encryption, the ransomware appends the .aac extension to all the affected files and then displays the Learn how to recover your files.txt file which has the ransom note, saying:
“It looks like your files have been encrypted.
If you are interested in your recovery, please contact us by email: [email protected]
Send your code to: [RANDOM HARACTERS]
Your request will be answered as soon as possible, and if necessary to guarantee recovery.”
Based on its message, it says that the file recovery will be guaranteed. But it’s really doubtful. You should know better than to trust cyber crooks, after all they’re not called cyber crooks for no reason.
In addition, even though the activity of the malware is low, many security tools can still identify it. It disguises under Generic.Ransom.XRatLocker.F09C48DD, Trojan/Win32.SGeneric, Trojan.Encoder.13028 trojan. And while the Xorist ransomware group is old, it is still persistent. Recently, its creators seem to be on the move again as several versions were released consecutively.
How is AAC’s malicious payload distributed?
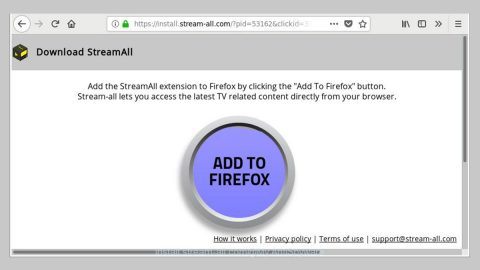
Since crypto-malware threats spread using different channels, you have to take preventive measures. As you probably know, most ransomware infections, AAC ransomware included, distribute their infection via spam emails. These spam emails has an infected attachment set to enter your computer once you open it. Do not fall into that trap even if you receive an email that is supposedly from FBI or other well-known groups and organizations for cyber crooks use this trick to lure you into opening the email and the attachment. The infected file could also be distributed through exploit kits, malicious redirect scripts, rogue applications, and other tools. For you to block out this ransomware’s assault, you have to be vigilant and keep your antivirus and system sleek by updating them always.
Eliminate AAC ransomware using the guidelines below.
Step 1: Open Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.

Step 2: Go to the Processes tab and look for any suspicious processes and then kill them.

Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 4: Look for AAC ransomware or any suspicious program and then Uninstall it/them.

Step 5: Hold down Windows + E keys simultaneously to open File Explorer.
Step 6: Go to the following paths and look for the ransomware’s malicious executable file and delete it.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %TEMP%
Step 7: After that, go to your desktop and every folder with encrypted files and look for the Learn how to recover your files.txt file and then delete them
Step 8: Close the File Explorer.
Step 9: Empty the Recycle Bin.
Step 10: Try to recover your encrypted files.
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if the malware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Follow the continued advanced steps below to ensure the removal of the AAC ransomware:
Perform a full system scan using SpyRemover Pro.
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK. - A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch SpyRemover Pro.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Pro to protect your computer from future threats.