What is Zuahahhah ransomware? And how does it work?
Zuahahhah ransomware is a ransomware Trojan that encrypts files leaving them inaccessible. This ransomware first emerged on July 28, 2017 and has since wreaked havoc on many users. It is a new version of the Crypt888 ransomware. The good thing is this variant isn’t that strong so it is decryptable.
Its malicious file, server.exe roams the web to infiltrate your computer. As soon as it gets onto your computer, it immediately establishes remote access with its Command and Control server to execute its attack. What’s more is that aside from obtaining information about your computer and operating system, this ransomware also tracks your information as well. So it isn’t hard to tell that one of Zuahahhah ransomware’s components might be a spyware.
After it establishes connection to its Command and Control server, it begins its main goal: to encrypt your files which aims on a bunch of popular types of files. Once it’s done encrypting your files, it quickly changes your PC’s desktop with its ransom note containing the following message:
“YOUR FILES HAS BEEN LOCKED
ZUAHAHHAH
Your Computer has been Get:
– password your account
– email account
– files your computer
– delete your files”
As you can see, the malware’s developers aren’t fluent in English. But the message they were trying to convey are pretty clear. This ransomware also has the ability to delete those encrypted files. Thus, you must remove this ransomware as soon as possible.
How is Zuahahhah ransomware spread online?
As mentioned earlier, this ransomware travels the web using a malicious executable file named server.exe. This infectious file spreads in an obfuscated email attachment. Cyber criminals often disguise the email as somewhat something of importance that you might feel the urge to open it out of curiosity. And that’s something you shouldn’t do because as we all know, curiosity kills the cat. So to avoid malware like Zuahahhah ransomware, make sure that you check the sender of the suspicious email first especially if it came from an unknown sender.
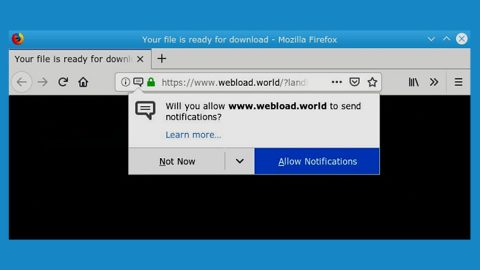
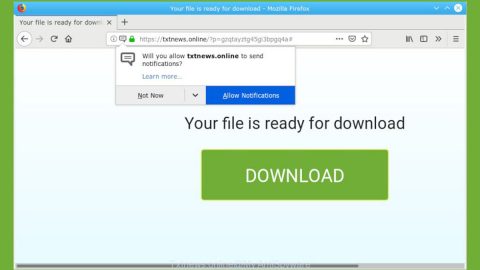
Aside from malicious email campaigns, the threat also spreads using the following techniques:
- Fake software & software updates
- Malvertising
- Exploit kits
To eliminate Zuahahhah, carefully follow the removal steps below.
Step 1: Open Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.

Step 2: Go to the Processes tab and look for any suspicious processes and then kill them.

Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for Zuahahhah Ransomware or any suspicious program and then Uninstall.

Step 5: Hold down Windows + E keys simultaneously to open Windows Explorer.
Step 6: Go to the directories listed below and delete everything in it. Or other directories you might have saved the file related to Zuahahhah Ransomware.
- %TEMP%
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step 7: Look for the ransomware’s malicious executable file which is server.exe as well as the shortcut file named Microsoft Update.lnk and delete them.
Step 8: After that, get rid of the ransom note which is the wallpaper in your desktop.
Step 9: Empty the Recycle Bin.
Step 10: Try to recover your encrypted files.
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if the malware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Follow the continued advanced steps below to ensure the removal of the Zuahahhah Ransomware:
Perform a full system scan using SpyRemover Pro.
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch SpyRemover Pro.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Pro to protect your computer from future threats.