What is GILLETTE ransomware? And how does it execute its attack?
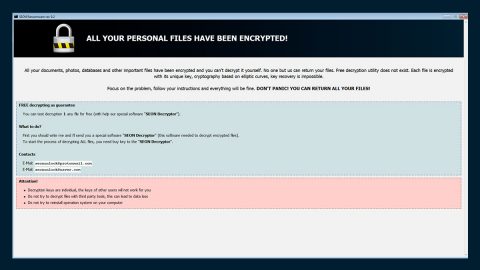
GILLETTE ransomware is a new cryptovirus that was discovered recently. It uses a “.GILLETTE” extension in marking the files it encrypts. Once its malicious payload is dropped in the system, it will connect to a Command & Control server controlled by its creators. This is where GILLETTE ransomware sends the information it gathers about the system.
From this server, it downloads its other malicious components and puts them into several system folders. They are used to manipulate system processes. They also scan the system for strings of certain programs like sandbox environment, virtual hosts, Firewall, and antivirus programs. Once it finds these programs, it disables or removes them to prevent them from interfering with the attack.
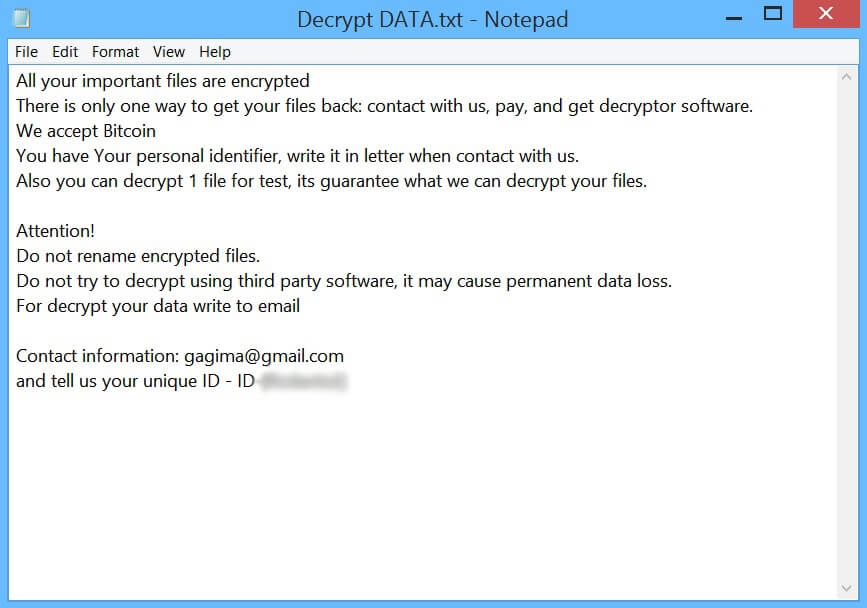
It also modifies the Windows Registry which affects some keys and sub-keys so that it can run automatically in every system boot. After that, it will start to encrypt important data in the system using an encryption algorithm. Once the file encryption is completed, GILLETTE ransomware also encrypts its own malicious components and appends the “.GILLETTE” extension to each one of the encrypted files and then releases a text file named “Decrypt DATA.txt” which contains the following message:
“All your important files are encrypted
There is only one way to get your files back: contact us, pay, and get decryptor software.
We accept Bitcoin
You have Your personal identifier, write it in a letter when contact with us.
Also, you can decrypt 1 file for the test, its guarantees what we can decrypt your files.
Attention!
Do not rename encrypted files.
Do not try to decrypt using third-party software, it may cause permanent data loss.
To decrypt your data write to the email
Contact information: [email protected]
and tell us your unique ID – ID-[REDACTED]”
Based on its ransom note, victims must contact the given email address ([email protected]) and pay the ransom. However, doing so is definitely not advised as these crooks might end up not giving you the decryptor after you pay the ransom. And besides, there are other alternative ways you can try to recover your files without spending any money.
How is the malicious payload of GILLETTE ransomware distributed online?
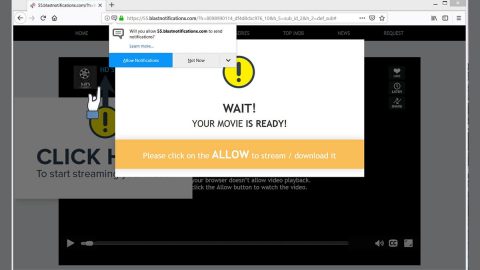
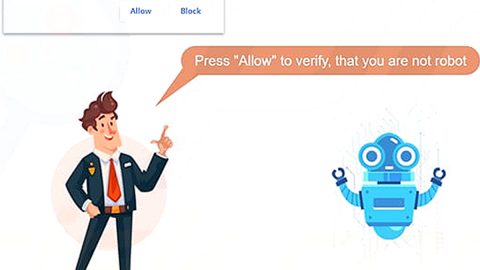
Creators of GILLETTE ransomware just like most ransomware developers uses malicious spam email campaigns in spreading this crypto-virus online. These malware-laden emails are often disguised to make it seem like the email was sent by some legitimate and well-known company or group to trick users into opening the email and downloading the attachment. Thus, you must always be cautious of downloading email attachments no matter who sent them.
Terminate GILLETTE ransomware from your computer with the help of the removal instructions provided below.
Step_1: the first thing you have to do is eliminate the processes of GILLETTE ransomware by opening the Task Manager. Just tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step_2: Next, go to the Processes tab and look for any suspicious-looking processes that could be related to GILLETTE ransomware and then right-click on it and select End Process or End Task.
Step_3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in “appwiz.cpl” and then click OK or press Enter.
Step_4: Look for dubious programs that might be related to GILLETTE ransomware and then Uninstall it/them.
Step_5: Close Control Panel and then tap Win + E to launch File Explorer.
Step_6: After opening File Explorer, navigate to the following directories below and look for GILLETTE ransomware’s malicious components such as Decrypt DATA.txt and [random].exe and other suspicious-looking files and then erase them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step_7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_8: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_9: Navigate to the listed paths below and look for the registry keys and sub-keys created by GILLETTE ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI\Background
- HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Personalization
- HKEY_CURRENT_USER\Control Panel\Desktop\ScreenSaveTimeOut
- HKEY_CURRENT_USER\Control Panel\Desktop
Step_10: Delete the registry keys and sub-keys created by GILLETTE ransomware.
Step_11: Close the Registry Editor.
Step_12: Empty your Recycle Bin.
Congratulations, you have just removed GILLETTE Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove GILLETTE Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
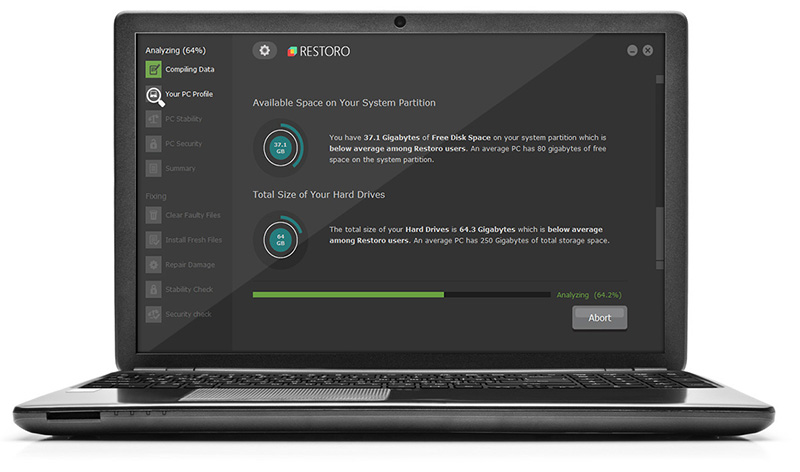
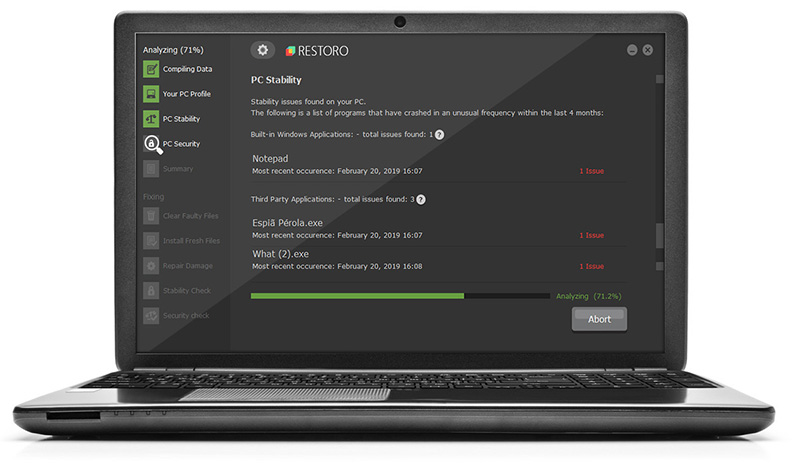
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.