What is Dragon ransomware? And how does it execute its attack?
Dragon ransomware is a newly-discovered variant of the Aurora ransomware which was first spotted in mid-August 2019. It uses a “.locked” extension in marking the files it encrypts. Apart from the extension it uses and its ransom note, another notable change in this new Aurora variant is the RSA 2048 cipher which it now uses in encrypting files.
The instant it executes its attack, a malicious payload is dropped in the system which activates the crypto-virus. From there, it establishes a connection to a remote Command and Control server controlled by the attackers. It may also employ an information-gathering module in order to obtain information about the infected PC and its user. The harvested data is then sent to the remote server where the ransomware downloads an additional malicious file that helps it in the execution of its attack.
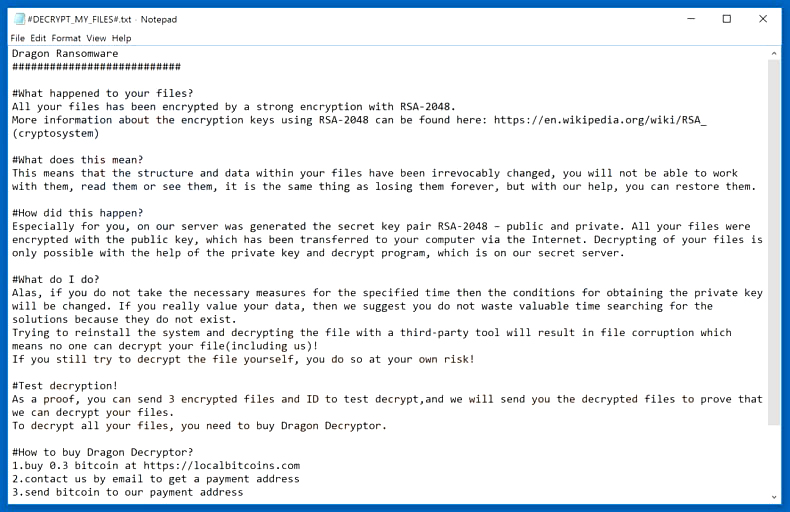
These malicious files are placed in the system folder which helps the crypto-malware from being detected by any antivirus programs or security software. Some of the malicious files also modify the Windows Registry which allows the crypto-malware to run on every system boot. After all these changes are applied, Dragon ransomware will start its search for targeted files to encrypt. Once it finds them, it applies the RSA 2048 encryption algorithm in locking the files. Following data encryption, it appends the “.locked” extension to each one of the encrypted files. It also releases a ransom note named “#DECRYPT_MY_FILES#.txt” that states:
“Dragon Ransomware
###########################
#What happened to your files?
All your files have been encrypted by a strong encryption with RSA-2048.
More information about the encryption keys using RSA-2048 can be found here: https://en.wikipedia.org/wiki/RSA_(cryptosystem)
#What does this mean?
This means that the structure and data within your files have been irrevocably changed, you will not be able to work with them, read them or see them, it is the same thing as losing them forever, but with our help, you can restore them.
#How did this happen?
Especially for you, on our server was generated the secret key pair RSA-2048 – public and private. All your files were encrypted with the public key, which has been transferred to your computer via the Internet. Decrypting of your files is only possible with the help of the private key and decrypt program, which is on our secret server.
#What do I do?
Alas, if you do not take the necessary measures for the specified time then the conditions for obtaining the private key will be changed. If you really value your data, then we suggest you do not waste valuable time searching for the solutions because they do not exist.
Trying to reinstall the system and decrypting the file with a third-party tool will result in file corruption which means no one can decrypt your file(including us)!
If you still try to decrypt the file yourself, you do so at your own risk!
#Test decryption!
As proof, you can send 3 encrypted files and ID to test decrypt, and we will send you the decrypted files to prove that we can decrypt your files.
To decrypt all your files, you need to buy Dragon Decryptor.
#How to buy Dragon Decryptor?
1. buy 0.3 bitcoin at https://localbitcoins.com
2. contact us by email to get a payment address
3. send bitcoin to our payment address
4. after payment, we will send you Dragon Decryptor
Email:
[email protected]”
How does Dragon ransomware proliferate?
At the time of writing, it isn’t clear yet how Dragon ransomware proliferates. However, it may spread like the other variants of Aurora ransomware which is via malicious spam email campaigns. Aside from spam emails, it may also spread via unprotected Remote Desktop Protocol, exploit kits, corrupted software cracks, and many more.
Obliterate Dragon ransomware from your computer with the help of the removal instructions laid out below.
Step_1: First, boot your computer into Safe Mode with Networking, and afterward, you have to terminate the malicious processes of Dragon ransomware using the Task Manager, and to open it, tap Ctrl + Shift + Esc keys.
Step_2: Go to the Processes tab and look for the malicious processes of Dragon ransomware like Dragon.exe, java.exe, icacls.exe, and conhost.exe and then right-click on it and select End Process or End Task.
Step_3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in “appwiz.cpl” and then click OK or press Enter.
Step_4: Look for dubious programs that might be related to Dragon ransomware and then Uninstall it/them.
Step_5: Close Control Panel and then tap Win + E to launch File Explorer.
Step_6: After opening File Explorer, navigate to the following directories below:
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step_7: From these directories, look for the malicious components of Dragon ransomware such as #DECRYPT_MY_FILES#.txt”, “Dragon.exe”, “javaw.exe”, “icacls.exe”, and “[random].exe” and then delete all of them
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_8: Close the File Explorer and tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_9: Navigate to the listed paths below and look for the registry keys and sub-keys created by Dragon ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_10: Delete the registry keys and sub-keys created by Dragon ransomware.
Step_11: Close the Registry Editor.
Step_12: Empty your Recycle Bin.
Try to recover your encrypted files using their Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if Dragon ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions and then click the Restore button.
Congratulations, you have just removed Dragon Ransomware Crypto-Malware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove Dragon Ransomware Crypto-Malware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
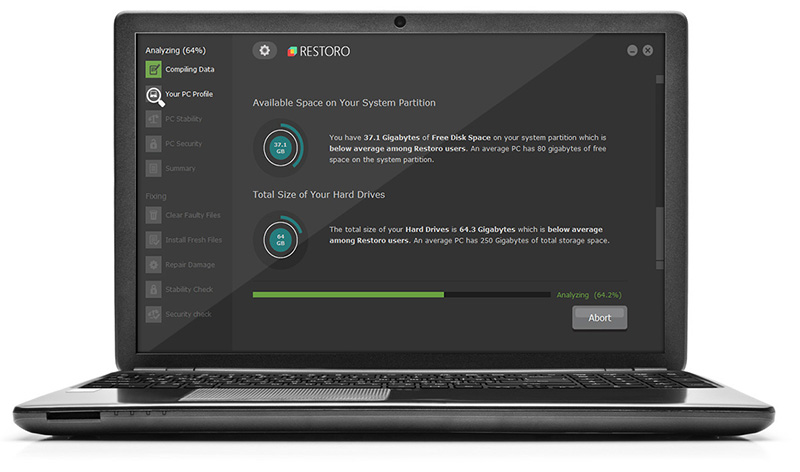
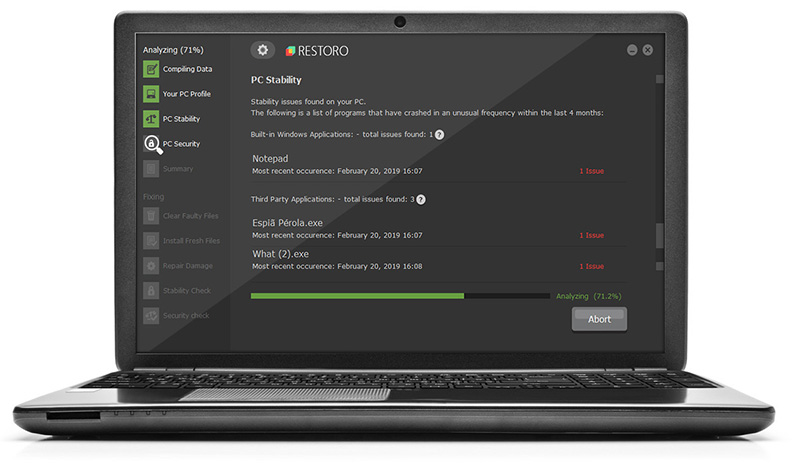
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.