What is BlackPink ransomware? And how does it implement its attack?
BlackPink ransomware is a file-encrypting virus designed to lock important data in a targeted computer. This newly discovered crypto-malware uses a “.BlackPink” extension in marking the files it encrypts. It seems to be targeting Korean-speaking users as its ransom note is written in the Korean language. At the time of writing, it isn’t clear yet if this new ransomware belongs to any ransomware group.
Once the payload file of BlackPink ransomware is executed, it will start to implement its attack by performing a series of modifications in the system. It also establishes a connection to a remote server controlled by cyber crooks behind this crypto-virus. This is where BlackPink ransomware downloads its malicious components which are placed on several system folders allowing BlackPink ransomware to repress or launch system processes. It generates a victim’s ID by collecting data from the infected system using a data gathering module. It also scans the computer for certain programs like firewalls, sandbox environments, virtual hosts, and antivirus programs that might interfere with the attack and if it finds them, it either removes or disables them.
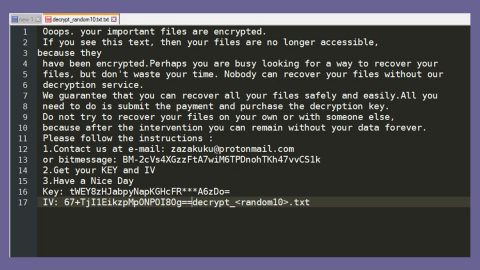
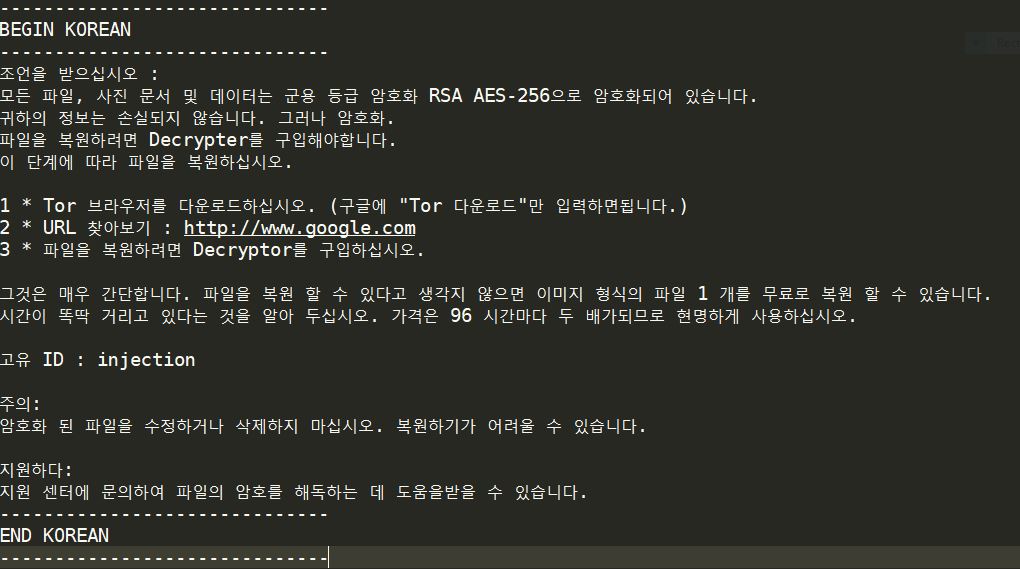
Moreover, BlackPink also modifies some registry keys and sub-keys in the Windows Registry allowing it to run automatically in every system boot, making it a persistent attack. Once it completes modifying system settings, BlackPink ransomware will start to encrypt its targeted files using AES 256 encryption algorithm. After the encryption, it opens a text file named “how_to_recover_files.txt” which contains the following message:
“——————————
BEGIN KOREAN
——————————
조언을 받으십시오 :
모든 파일, 사진 문서 및 데이터는 군용 등급 암호화 RSA AES-256으로 암호화되어 있습니다.
귀하의 정보는 손실되지 않습니다. 그러나 암호화.
파일을 복원하려면 Decrypter를 구입해야합니다.
이 단계에 따라 파일을 복원하십시오.
1 * Tor 브라우저를 다운로드하십시오. (구글에 “Tor 다운로드”만 입력하면됩니다.)
2 * URL 찾아보기 : http://www.google.com
3 * 파일을 복원하려면 Decryptor를 구입하십시오.
그것은 매우 간단합니다. 파일을 복원 할 수 있다고 생각지 않으면 이미지 형식의 파일 1 개를 무료로 복원 할 수 있습니다.
시간이 똑딱 거리고 있다는 것을 알아 두십시오. 가격은 96 시간마다 두 배가되므로 현명하게 사용하십시오.
고유 ID : injection
주의:
암호화 된 파일을 수정하거나 삭제하지 마십시오. 복원하기가 어려울 수 있습니다.
지원하다:
지원 센터에 문의하여 파일의 암호를 해독하는 데 도움을받을 수 있습니다.
——————————
END KOREAN
——————————”
How does BlackPink ransomware proliferate?
Since BlackPink ransomware is relatively new, its distribution method is still unknown. However, it may proliferate using common distribution methods like malicious spam email campaigns. Cybercriminals usually attack infected links or files in emails. And once the infected link is clicked or once the infected file is opened, it will launch BlackPink ransomware in the system.
Obliterate BlackPink ransomware from your computer with the help of the removal guide below.
Step_1: You have to terminate the malicious processes of BlackPink ransomware first using the Task Manager and to open it, tap Ctrl + Shift + Esc keys.
Step_2: Go to the Processes tab and look for any malicious processes that could be related to BlackPink ransomware and then right-click on each one of them and select End Process or End Task.
Step_3: Close the Task Manager and open the Programs and Features section in Control Panel by pressing the Windows key + R, then type in “appwiz.cpl” and then click OK or press Enter.
Step_4: Look for dubious programs that might be related to BlackPink ransomware and then Uninstall it/them.
Step_5: Close Control Panel and then tap Win + E to launch File Explorer.
Step_6: After opening File Explorer, navigate to the following directories below and look for BlackPink ransomware’s malicious components such as how_to_recover_files.txt, and [random].exe, as well as other suspicious-looking files and then erase them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step_7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_8: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_9: Navigate to the listed paths below and look for the registry keys and sub-keys created by BlackPink ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI\Background
- HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Personalization
- HKEY_CURRENT_USER\Control Panel\Desktop\ScreenSaveTimeOut
- HKEY_CURRENT_USER\Control Panel\Desktop
Step_10: Delete the registry keys and sub-keys created by BlackPink ransomware.
Step_11: Close the Registry Editor.
Step_12: Empty your Recycle Bin.
Try to recover your encrypted files using their Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if BlackPink ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Congratulations, you have just removed BlackPink Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove BlackPink Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
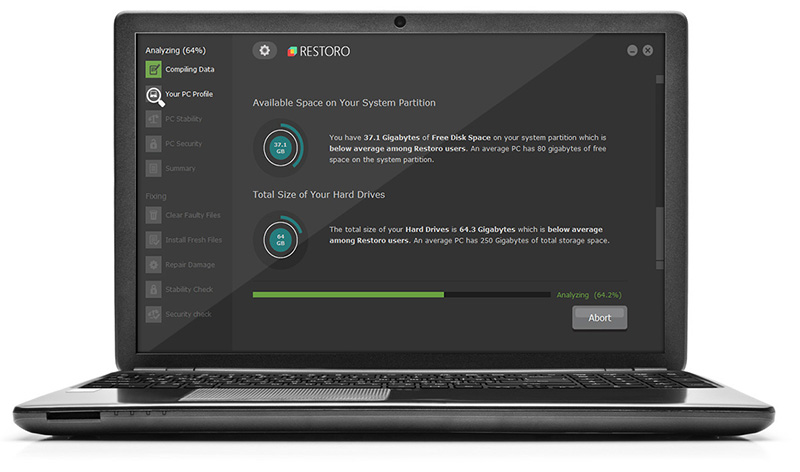
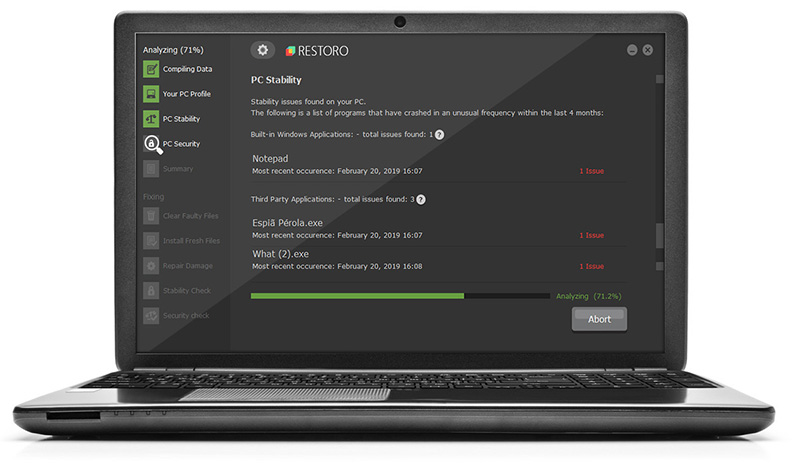
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.