What is GermanWiper ransomware? And how does it carry out its attack?
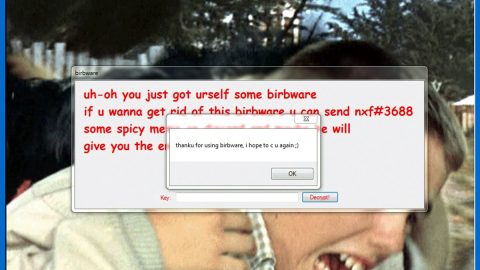
GermanWiper ransomware is a newly discovered dangerous threat that’s been targeting German users. Unlike other ransomware threats, GermanWiper ransomware does not encrypt files but overwrites them with zero bytes. As a result, the affected files will no longer be accessible or usable and will become empty. It adds 5 random characters to each one of the files.
The instant its payload file is dropped in the system, GermanWiper ransomware will launch itself using PowerShell commands. After that, it will establish a connection to a remote server controlled by the attackers. It then proceeds to modify essential system settings in order to automatically run each time the infected computer is started. Later on, it rewrites tons of files in the system with a zero-based code that leads to permanent loss of data. It pretends to encrypt files by adding several 5 random characters to the compromised files.
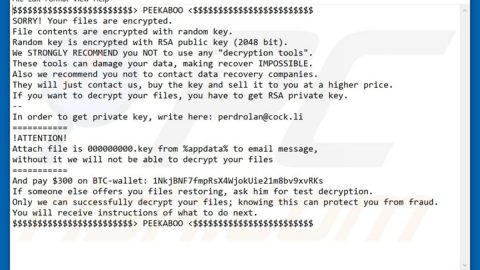
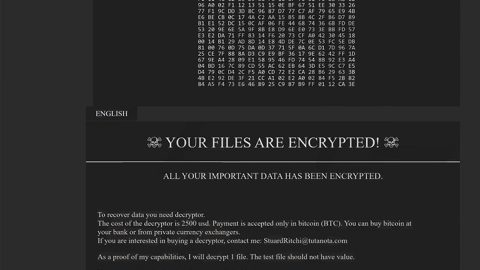
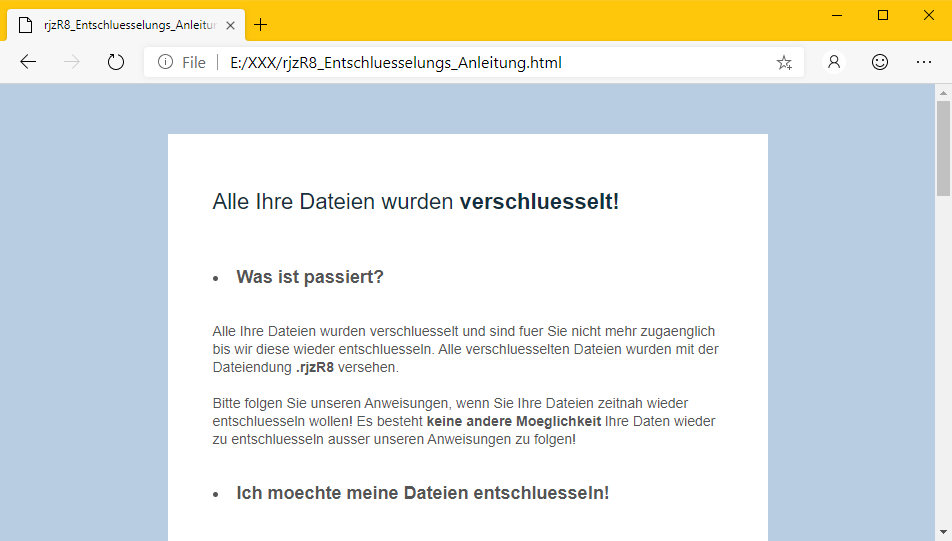
Cyber crooks behind this threat claim that the compromised files can be recovered by paying the ransom demanded as stated in its ransom note named _Entschluesselungs_Anleitung.html which is quite lengthy. Here are some parts of its ransom note:
“Alle Ihre Dateien wurden verschluesselt!
Was ist passiert?
Alle Ihre Dateien wurden verschluesselt und sind fuer Sie nicht mehr zugaenglich bis wir diese wieder entschluesseln. Alle verschluesselten Dateien wurden mit der Dateiendung .phnB2 versehen.
Bitte folgen Sie unseren Anweisungen, wenn Sie Ihre Dateien zeitnah wieder entschluesseln wollen! Es besteht keine andere Moeglichkeit Ihre Daten wieder zu entschluesseln ausser unseren Anweisungen zu folgen!
Ich moechte meine Dateien entschluesseln!
Kein Problem! Um Ihre Dateien zu entschluesseln, benoetigen Sie unsere Entschluesselungssoftware, diese steht zum Kauf fuer umgerechnet ca. $1,500 bereit.
Der Betrag ist ausschliesslich in Bitcoin an die untenstehende Adresse zu zahlen.
Welche Garantien habe ich?
Uns interessiert nicht wer Sie sind oder was fuer Dateien Sie auf Ihrem Computer haben, wir sind ausschliesslich daran interessiert Ihnen die Entschluesselungssoftware zu verkaufen. Schlechtes Business spricht sich herum, sollten wir Ihre Dateien nicht entschluesseln, wuerde in Zukunft niemand unsere Entschluesselungssoftware kaufen – Was nicht in unserem Interesse liegt.
Wo bekomme ich Bitcoins?
Bitcoin koennen Sie schnell und einfach kaufen, z.B mit Kreditkarte, GiroPay oder (SOFORT) Ueberweisung. Es folgt eine Auflistung populaerer Tauschboersen und Bitcoin Marktplaetzen:
Coinmama – hxxps://coinmama.com/
Bitpanda – hxxps://www.bitpanda.com/
AnyCoinDirect – hxxps://anycoindirect.eu/
Bitcoin.de – hxxps://www.bitcoin.de/
BTC Direct – hxxps://btcdirect.eu/de-at
Es gibt noch weitere moeglichkeiten Bitcoin zu erwerben, sollte keine der gelisteten fuer Sie funktionieren, hilft Ihnen eine kurze Google Suche.
Ich habe die Bitcoins gekauft
Senden Sie den folgenden Betrag an die fuer Sie generierte Bitcoin Adresse:
Betrag
0.15038835 Bitcoin
Bitcoin Adresse
17vH1YT63jRTavNQRGGsP49xjzZtZsxNRF”
How does GermanWiper ransomware proliferate?
According to security experts, GermanWiper ransomware spreads via malicious spam email campaigns. These malware-infested emails claim to be job applications from a person named “Lena Kretschmer”. It contains an attached “CV” which is a ZIP file that has an LNK shortcut file. This file once opened, will install GermanWiper ransomware in the targeted system.
Make sure that you carefully follow the given removal guide below to successfully wipe out GermanWiper ransomware from your computer.
Step_1: Restart your PC and boot into Safe Mode with Command Prompt by pressing F8 a couple of times until the Advanced Options menu appears.
Step_2: Navigate to Safe Mode with Command Prompt using the arrow keys on your keyboard. After selecting Safe Mode with Command Prompt, hit Enter.
Step_3: After loading the Command Prompt type cd restore and hit Enter.
Step_4: After cd restore, type in rstrui.exe and hit Enter.
Step_5: A new window will appear, and then click Next.
Step_6: Select any of the Restore Points on the list and click Next. This will restore your computer to its previous state before being infected with GermanWiper Ransomware. A dialog box will appear and then click Yes.
Step_7: After System Restore has been completed, try to enable the disabled Windows services.
- Press Win + R keys to launch Run.
- Type in MSC in the box and press Enter to open Group Policy.
- Under Group Policy, navigate to:
- User Configuration\Administrative Templates\System
- After that, open Prevent access to the command prompt.
- Select Disable to enable cmd
- Click the OK button
- After that, go to:
- Configuration\Administrative Templates\System
- Double click on the Prevent Access to registry editing tools.
- Choose Disabled and click OK.
- Navigate to :
- User Configuration\Administrative Templates\System>Ctrl+Alt+Del Options
- Double click on Remove Task Manager.
- And then set its value to Disabled.
Step_8: Next, tap Ctrl + Shift + Esc to open the Task Manager and then go to the Processes tab and look for the malicious processes of GermanWiper Ransomware and end them all.
Step_9: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK to open the list of installed programs. From there, look for GermanWiper ransomware or any malicious program and then Uninstall it.
Step_10: Tap Windows + E keys to open the File Explorer then navigate to the following directories and delete the malicious files created by GermanWiper ransomware such as _Entschluesselungs_Anleitung.html, ctNfy_Entschluesselungs_Anleitung.html, eRq7E_Entschluesselungs_Anleitung.html, RadEW_Entschluesselungs_Anleitung.html and [random].exe, as well as the ZIP file.
- %UserProfile%\AppData
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
- %TEMP%.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step_11: Close the File Explorer.
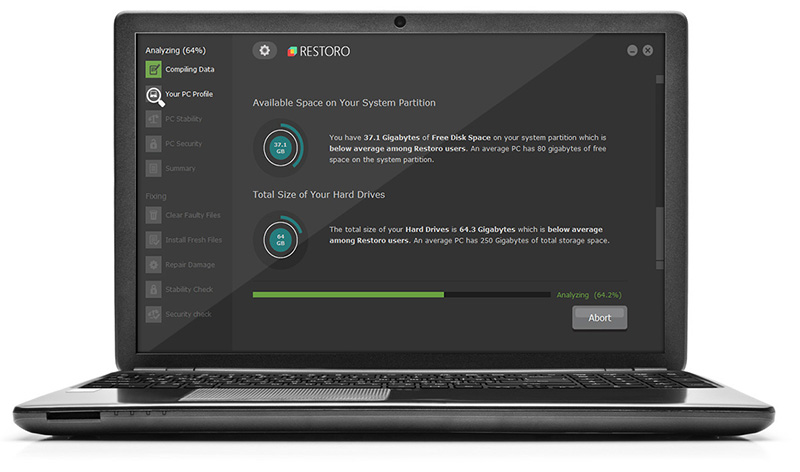
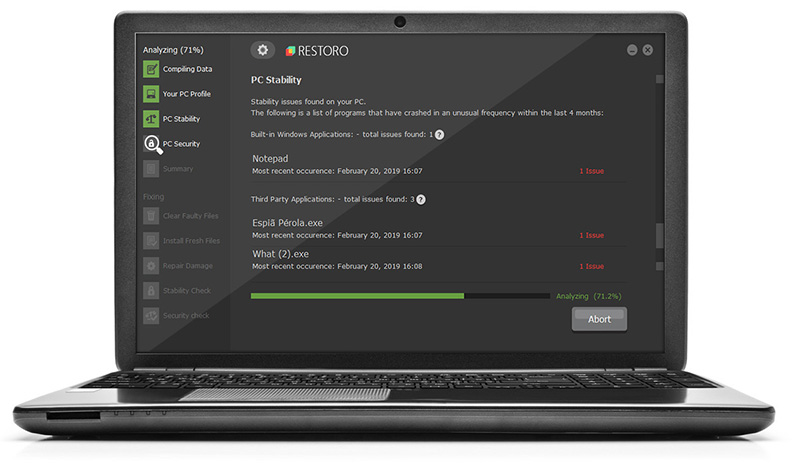
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_12: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_13: Navigate to the paths listed below and delete all the registry values added by GermanWiper ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_14: Close the Registry Editor and empty your Recycle Bin.
Congratulations, you have just removed GermanWiper Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove GermanWiper Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.