What is Scarab crab ransomware? And how does it implement its attack?
Scarab crab ransomware is the latest addition to the Scarab ransomware family. This new Scarab variant seems to imitate GandCrab ransomware as it uses the .crab extension in marking its encrypted files. However, aside from the identical extension, it does not have other similarities with GandCrab ransomware. At the time of writing, it isn’t known who the group behind this ransomware is. However, security experts speculated that the crooks might have accessed the original source code of Scarab ransomware.
When it comes to its attack, Scarab crab ransomware still uses the same pattern as other Scarab ransomware variants. Once its malicious payload is dropped in the system, it starts to implement its attack by using a data gathering module used to obtain information about the system and its user. The harvested data is then used for another module called stealth protection which is used to apply a signature scan that detects any antivirus programs, virtual machine hosts, and sandbox environments and prevents them from interfering with the attack. Shortly after these modules are implemented, Scarab crab ransomware will begin encrypting its targeted data that are mostly user-generated such as files with the following extensions:
.PNG .PSD .PSPIMAGE .TGA .THM .TIF .TIFF .YUV .AI .EPS .PS .SVG .INDD .PCT .PDF .XLR .XLS .XLSX .ACCDB .DB .DBF .MDB .PDB .SQL .APK .APP .BAT .CGI .COM .EXE .GADGET .JAR .PIF .WSF .DEM .GAM .NES .ROM .SAV CAD Files .DWG .DXF GIS Files .GPX .KML .KMZ .ASP .ASPX .CER .CFM .CSR .CSS .HTM .HTML .JS .JSP .PHP .RSS .XHTML. DOC .DOCX .LOG .MSG .ODT .PAGES .RTF .TEX .TXT .WPD .WPS .CSV .DAT .GED .KEY .KEYCHAIN .PPS .PPT .PPTX ..INI .PRF Encoded Files .HQX .MIM .UUE .7Z .CBR .DEB .GZ .PKG .RAR .RPM .SITX .TAR.GZ .ZIP .ZIPX .BIN .CUE .DMG .ISO .MDF .TOAST .VCD SDF .TAR .TAX2014 .TAX2015 .VCF .XML Audio Files .AIF .IFF .M3U .M4A .MID .MP3 .MPA .WAV .WMA Video Files .3G2 .3GP .ASF .AVI .FLV .M4V .MOV .MP4 .MPG .RM .SRT .SWF .VOB .WMV 3D .3DM .3DS .MAX .OBJ R.BMP .DDS .GIF .JPG .CRX .PLUGIN .FNT .FON .OTF .TTF .CAB .CPL .CUR .DESKTHEMEPACK .DLL .DMP .DRV .ICNS .ICO .LNK .SYS .CFG
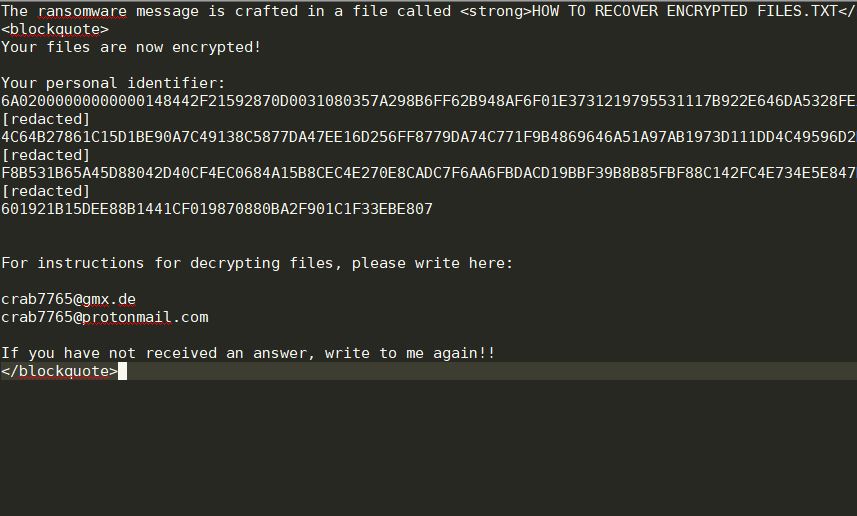
Following data encryption, Scarab crab ransomware opens a file named “HOW TO RECOVER ENCRYPTED FILES.txt” which contains the following message:
“Your files are now encrypted!
Your personal identifier:
6A02000000000000148442F21592870D0031080357A298B6FF62B948AF6F01E3731219795531117B922E646DA5328FEACDF6
509810777DEEIA676A5418BE327SF7BIDDBDC686577729F18SDlESSC9333BAB818BA7D4FECA80196368184ACACB6C559C888
4C64B27861C15D1BE90A7C49138C5877DA47EE16D256FF8779DA74C771F9B4869646A51A97AB1973D111DD4C49596D2E8D
058608680498563883E279661F21E38A74841885895908A7EI75F783AA93A1254875900809A901ECCE456218C5638231353KG
F8B531B65A45D88042D40CF4EC0684A15B8CEC4E270E8CADC7F6AA6FBDACD19BBF39B8B85FBF88C142FC4E734E5E847E8A7E
2FBAB24416860BCBCCFBA5014927EAEDlBSDA5F85CB2A1EBDB56510539496579399A1C3896SF908FD4488EE7628FDFDB7BA5
601921B15DEE88B1441CF019870880BA2F901C1F33EBE807
For instructions for decrypting files, please write here:
[email protected]
[email protected]
If you have not received an answer, write to me again!”
How is the malicious payload of Scarab crab ransomware disseminated online?
The malicious payload of Scarab crab ransomware may be disseminated using several methods such as a payload dropper which initiates the malicious script used to install the crypto-malware in the system.
To obliterate Scarab crab ransomware from your computer, follow the removal instructions below.
Step_1: Tap the Ctrl + Alt + Delete keys to open a menu and then expand the Shutdown options which are right next to the power button.
Step_2: After that, tap and hold the Shift key and then click on Restart.
Step_3: And in the Troubleshoot menu that opens, click on the Advanced options and then go to the Startup settings.
Step_4: Click on Restart and tap F4 to select Safe Mode or tap F5 to select Safe Mode with Networking.
Step_5: After your PC has successfully rebooted, tap Ctrl + Shift + Esc to open the Task Manager.
Step_6: Go to the Processes tab and look for any suspicious-looking processes that could be related to Scarab crab ransomware and then end their processes.
Step_7: Exit the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step_8: Look for suspicious programs that could be related to Scarab crab ransomware and then uninstall them.
Step_9: Close the Control Panel and tap Win + E keys to open File Explorer.
Step_10: Navigate to the following locations and look for the malicious components created by Scarab crab ransomware like “HOW TO RECOVER ENCRYPTED FILES.txt” and “Initiatives” then make sure to delete them all.
- %APPDATA%
- %TEMP%
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step_11: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use Restoro this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_12: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_13: Navigate to the listed paths below and look for the registry keys and sub-keys created by Scarab crab ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_14: Delete the registry keys and sub-keys created by Scarab crab ransomware.
Step_15: Close the Registry Editor and empty the contents of the Recycle Bin.
Congratulations, you have just removed Scarab crab Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
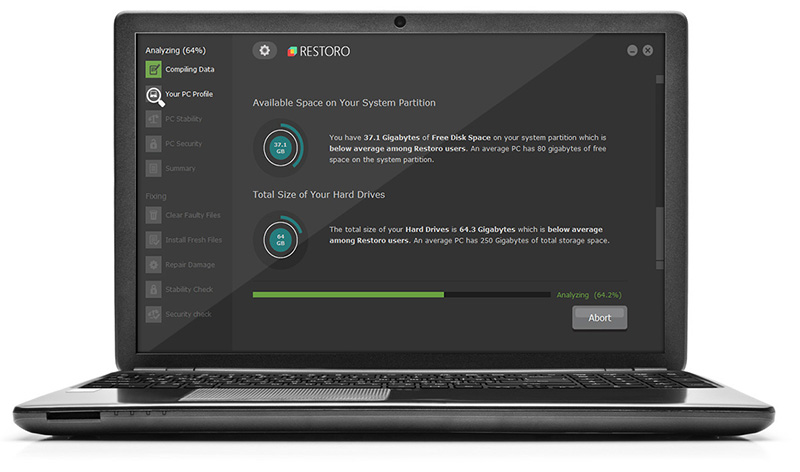
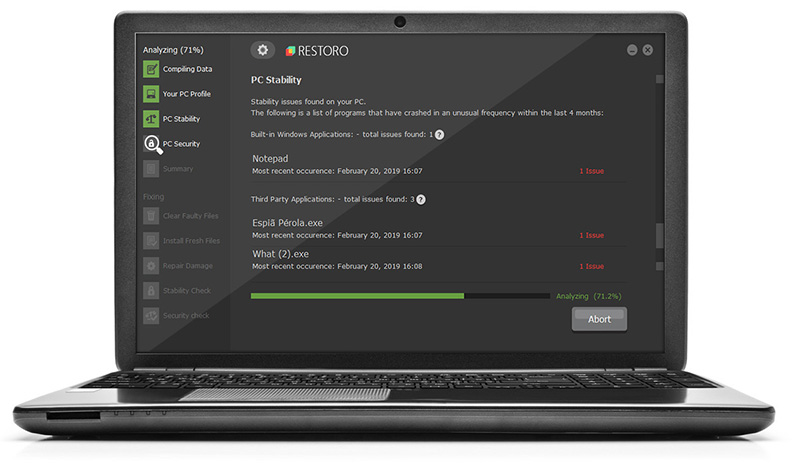
Now that’s how you remove Scarab crab Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.