What is Dangerous ransomware? And how dangerous can it really be?
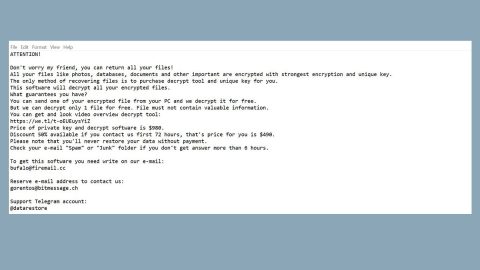
Dangerous ransomware is a crypto-malware aiming to encrypt files in a targeted PC. As soon as it enters the system, it will start to encode data making them inaccessible without the decryption key. On each of the encrypted files, the ransomware appends the .wtf extension. It then drops its ransom note in a file named HOWTODECRYPTFILES.html which contains the following message”
“Dangerous Ransomware
To decrypt the files, you need to purchase special software Dangerous decryptor
Restore the data, follow the instructions!
You can learn more / request
e-mail: [email protected]
You can learn more/questions in the chat:
hxxp://kuysqebjbttaxmq2.onion.to (not need Tor)
hxxps://kuysqebjbttaxmq2.onion.cab (not need Tor)
hxxp://kuysqebjbttaxmq2.onion/ (need Tor)
You can learn more problem out bitmessage:
hxxps://bitmsg.me/ BM-2cTFScArDZfPNYbefeDn1RJL44NkvuVPr
If the resource is unavailable for a long time to install and use the terms of reference of the browser:
- + Start the Internet browser
- + Type or copy the address https://www.torproject.org/download/download-easy.html in the address bar of your browser and press key ENTER
- + On the website you will be prompted to download the Tor browser, download and install it. To work.
- + Connection, click “connect” (using English version)
- + After connecting, open a normal window Tor-browser
- + Type or copy the address http://kuysqebjbttaxmq2.onion/ in the address bar of Tor-browser and press key ENTER
- + Wait for the download site
+ If you have any problems with installation or usage, please visit the video:
- Your personal identification ID:[redacted]”
Although the ransom amount is not indicated on its ransom note, there is still no need for you to reach to these crooks and pay the ransom as you will only waste both your time and money. You could try out other alternative ways to recover the encrypted files such as using their shadow volume copies. As long as the ransomware hasn’t deleted the shadow volume copies of the files, you’ll do just fine.
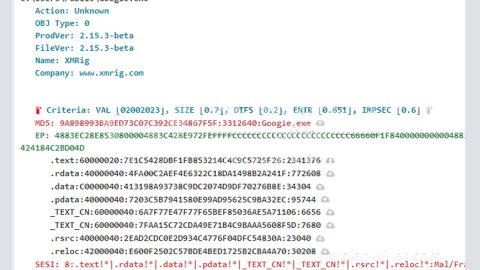
How does Dangerous ransomware infiltrate a system?
The cybercriminals behind Dangerous ransomware employ deceptive distribution techniques to spread Dangerous ransomware. One of the distribution methods it uses is through spam emails where the crooks attach a corrupted file used to download and install Dangerous ransomware from a remote server. To prevent getting caught off guard by this ransomware threat or any computer threats for that matter, it would be better if you always update both your antivirus program and system.
Kill Dangerous ransomware from your PC using the steps below.
Step 1: Close the ransom note of Dangerous ransomware and tap the Win + E keys to open File Explorer.
Step 2: Navigate to the following locations and look for the malicious files created by Dangerous ransomware such as HOWTODECRYPTFILES.html, and other suspicious-looking files and delete them al.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- %HOMEDRIVE%\user | ransom.jpg
- %USERPROFILE%\Desktop | READ_IT.txt
Step 3: Close the File Explorer and tap Ctrl + Shift + Esc keys to open the Task Manager.

Step 4: After opening the Task Manager, look for Dangerous ransomware’s malicious process, right click on it and select End Process or End Task.

Step 5: Close the Task Manager.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step 6: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 7: Navigate to the following path:
HKU\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
Step 8: Look for any suspicious values created by Dangerous ransomware and delete them.
Step 9: Close the Registry Editor and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 10: Look for Dangerous ransomware or any suspicious program and then Uninstall it/them.

Step 11: Empty your Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if Dangerous ransomware hasn’t deleted the shadow volume copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Ensure the removal of Dangerous ransowmare from your computer as well as the malicious files it created with the help of the advanced removal instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen willbe displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. The installation will start automatically once a download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.