What is OopsLocker ransomware? And how does it work?
OopsLocker ransomware is a crypto-threat which is a new variant of the recently discovered Oops ransomware. This ransomware employs a combination of two encryption algorithms: the AES and RSA 2048 cryptographies. The contents on your computer is encrypted with the customized AES cipher while the decryption key is encrypted with the RSA 2048 cipher which prevents cyber security researchers in coming up with a decryptor. After it infiltrates your computer, it executes a task to enable it to communicate to its Command and Control server. From there, the ransomware sends particular information about the infected computer to the remote C&C server. The information sent out consists of the following:
- Your computer’s protections and antivirus program
- Your Windows operating system version
- The keyboard setup
- And your IP address
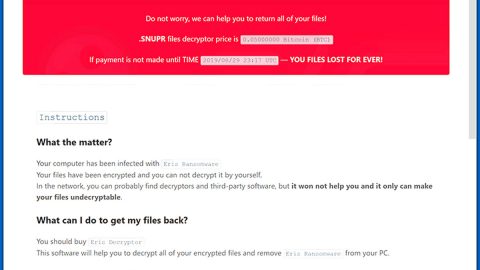
After OopsLocker ransomware settles in, it will start to scan the computer’s system to look for different file types which is over 40 file types including Microsoft Word documents, images, videos, mp3 files, databases, etc. It then starts the encryption process and appends the .oops file extension. Once it completed the encryption, it drops a file named EncryptedFiles.txt that contains the list of encrypted files and is placed on the folder named ProgramData in C that also have the EncryptedKey and KeyHash files. And then it opens an executable file, oops.exe containing the ransom notification that has the following text:
“Oops, all data in your computer has been encrypted.
Your encrypted key file is: C: \PrograrnData\oops\EncryptedKey
Your computer name is: [ACTIVE USER ACCOUNT NAME]
If you wanna decrypt all your data, please send 0.1 bitcoin to the address:
1FMvaobyrMNzVqeabC4hPumpbG1iGHo7m5
But BEFORE you pay me, you should send me an email with the ENCRYPTED KEY FILE as an attachment, YOUR COMPUTER NAME and BITCOIN ADDRESS you will pay with. So that i can know it’s your payment.
My email address is: only4you@protonmail. com
After i confirm the payment, i’ll send you an email with your KEY and COMPUTER NAME for decryption, you can input it below, and decrypt.”
The cyber criminals will threaten you that you should keep oops.exe running on your system if you are interested in paying the ransom to recover your files. They also require you to pay 0.1 Bitcoin which is approximately $233 according to the conversion rates at the time of writing this article. However, the crooks might extort more money than the amount stated.
How is OopsLocker ransomware distributed?
Just like the Oops ransomware, OopsLocker ransomware also spreads through spam emails. Its malicious file is disguised as a regular Microsoft Word file which contains macro-enabled commands used in carrying out its attack. So when you open this malicious document, you will receive a pop-up that alerts you to enable macros to view the content of the file. When you enable this, that’s where the ransomware starts its infiltration.
Take note that these emails may look like they’re from a well-known company or government organizations to make it believable and to attract your attention. There is no doubt that cyber criminals these days are getting cleverer in distributing their malicious files so you have to be cautious when you open files from unknown senders, well-known company or not.
To eliminate OopsLocker ransomware, be sure to carefully follow the steps below:
Step 1: Close the oops.exe window.
Step 2: Reboot your computer into Safe Mode
Windows XP/Vista/7
- Reboot your computer.
- Tap F8 when you see the BIOS screen.
- Select Safe Mode from the Advanced Boot Options menu using the arrow keys on your keyboard.
- Press Enter.
- And then proceed to remove the OopsLocker ransomware.
Windows 8/8.1/10
- Tap two buttons: the Windows key and C on your keyboard and click Settings (if you use Windows 8/8.1) or click on the Start button (if you use Windows 10).
- Click Power.
- Hold the Shift key and click Restart.
- Click Troubleshoot.
- Click Advanced options.
- Click Startup Settings.
- Click on the Restart button.
- Tap F4.
- Proceed removing the OopsLocker ransomware when your PC starts in Safe Mode.
Step 3: Open the Windows Task Manager by pressing Ctrl + Shift + Esc at the same time. Proceed to the Processes tab and look for oops.exe or any suspicious processes that can be related to the OopsLocker Ransomware.

Right-click on the processes, then click Open File Location and scan them using a powerful and trusted antivirus like SpyRemover Pro. After opening their folders, end their processes and delete their folders. If the virus scanner fails to detect something that you know is suspicious, don’t hesitate to delete it.
Step 4: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK.

Look for OopsLocker ransomware or any suspicious program and then Uninstall.

Step 5: Hold down Windows + E keys simultaneously to open File Explorer.
Step 6: Go to the directories listed below and delete everything in it. Or other directories you might have saved the file related to OopsLocker ransomware.
- C:\ProgramData\oops
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %Temp%.
Step 7: Look for oops.exe and the following malicious components of OopsLocker ransomware and then delete all of them.
- txt
- EncryptedKey
- KeyHash
The next step below is not recommended for you if you don’t know how to navigate the Registry Editor. Making registry changes can highly impact your computer. So it is highly advised to use PC Cleaner Pro instead to get rid of the entries that OopsLocker ransomware created. So if you are not familiar with the Windows Registry skip to Step 12 onwards.

However, if you are well-versed in making registry adjustments, then you can proceed to step 8.
Step 8: Open the Registry Editor, to do so, tap Win + R and type in regedit and then press enter.
Step 9: Navigate to the path below:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Step 10: Delete the any suspicious registry value.
Step 11: Close the Registry Editor.
Step 12: Empty the Recycle Bin.
Follow the continued advanced steps below to ensure the removal of the OopsLocker ransomware:
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOSscreen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Optionuse the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Boxwill show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch SpyRemover Pro.
- Run SpyRemover Proand perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Proto protect your computer from future threats.