Untabs Virus Extension (Adware/Browser Hijackers)

It is indeed unpleasant experience when your Chrome, Firefox, IE or whatever other type of browser you might be using infiltrated by some strange, unfamiliar and fishy piece of software that seems to be executing certain tasks that it was not permitted to, and which becomes annoying as it goes. These types of programs are normally referred to as Browser Hijackers and this Untabs Virus Extension is one of them. Usually, the users with this piece of software installed on their computer report that it has changed their browser’s front page as well as that it has installed some new obscure search engine on the browser replacing the default one with it. Other than that, Untabs Virus Extension tends to trigger page redirects or generate pesky pop-ups that worsen and obstruct one’s browsing experience.
What are Untabs Virus Extension Browser Hijackers primarily used for?
Obviously, most programs similar to adware or hijacker Untabs Virus would hardly ever provide the user with any actual form of helpful or beneficial function. Of course, there are exceptions and some instances that this annoying program might actually prove to contain some actual use but this is hardly ever the case. It is revealed that Browser Hijackers are purposely designed for generating income for their creators by implementing and exploiting a variety of different techniques that mostly have something to do with the online marketing industry. However, the problem with Hijackers isn’t only that they can be extremely annoying and irritating and brings hassle, but also that in certain situations, they can potentially compromise your system’s security especially if you aren’t careful around them.
Why are these dangerous?
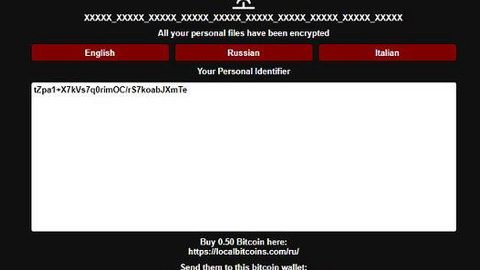
Firstly, we ought to let you know that this Untabs Virus and the like and not real computer viruses. But many of the researchers considered them as malware, Hijackers are nowhere near as problematic or as harmful as viruses the likes of Trojan Horses, Ransomware, Spyware, and the like. A typical Hijacker wouldn’t try to mess with the files that are on its hard-drive or even harm your system. But, certain security weaknesses and exploits might get triggered due to the Hijacker’s presence on your system and through redirects, and it is one important thing to be careful with is the potential page redirects and pop-ups that some of those programs might generate. So definitely do not interact with them, it is very inadvisable since you never know what site may open and what its contents may be. Generally, if you think that you have a Hijacker on your computer, then you should avoid clicking on anything that might come from it and also invest in unwanted software removal tool and get rid of it ASAP.
How do you get the infection and how can you prevent it?
Unlike the other malware, the Untabs Virus is actually quite innocent if compared to actual viruses such as the infamous Trojan Horses or the insidious Ransomware. But, if you do not learn how to protect your computer system against potentially unwanted and hazardous software, you might end up landing all sorts of nasty and pesky programs that could cause way more problems than a Hijacker. You probably already know that the most frequently employed methods for spreading such types if undesirable software or even the other malware is through spam e-mails- these are an extremely popular tool for distributing shady applications so make sure to avoid opening any sketchy online letters that you might receive. Also keep in mind that not all Internet ads that you see are safe. In fact, a large portion of the pop-ups, banners and box messages that might appear in your browser are actually serve as redirect links to all sorts of unreliable, questionable sites that might be dangerous to your computer’s security. Another is, we strongly advise you to stay away from any web-addresses that you do not seem to be trusted, that simple. Lastly, never install anything on your computer before checking the setup wizard for application bundles, because oftentimes Hijackers and other forms of unwanted software get added to the installers of other programs and get installed bundled along them if not unchecked from the setup menu. Do not make that mistake ever or you’ll regret it sooner than your think! Better yet, remove it completely from the system as soon as you are able.
How to remove Untabs Viruses?
Step 1: Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Step 2: Since manual removal takes hours and may damage your system in the process. For a safe removal solution, use SpyRemover Pro
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:
“use a one click solution like SpyRemover Pro”
After you open their folder, end the processes that are infected, then delete their folders.
Step 3: Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:
Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
Step 4: Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.
- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

Step 6:
Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random