What is Cyberresearcher ransomware? And how does it execute its attack?
Cyberresearcher ransomware is a new ransomware Trojan discovered in the second week of April 2018. This new ransomware threat is created based on the HiddenTear ransomware, an open source platform commonly used by cyber crooks in creating similar threats. According to security experts, Cyberresearcher ransomware seems to function similarly to Scarab ransomware and Balbaz ransomware. Once this crypto-virus is able to infect a system, it scans it for the following file types to encrypt:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip
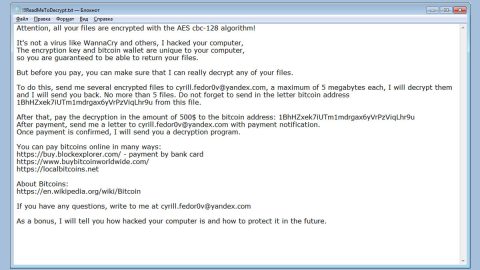
Just like most ransomware threats created using HiddenTear, Cyberresearcher ransomware uses the AES cipher in locking its targeted files. After the encryption, it appends the .CYBERRESEARCHER extension to the encrypted files and drops a file named “READ_IT.html” that states:
“CYBERRESEARCHER
Your files have been encrypted by CYBERRESEARCHER
Send 2.5 Bitcoins to 126HY2x4gBWDxzff3PRi8hrcqoHpgNSvr6
Your files will be deleted permanently if the Bitcoins are not sent in the next 48 hours”
Based on its ransom note, cybercriminals behind Cyberresearcher ransomware asks for 2.5 Bitcoins which is approximately $20000. This ransom amount is ridiculously huge and even if it were at an affordable price, you should still not pay the ransom as these crooks tend to ignore their victims once they receive the payment. The best thing you could do is try out other alternative methods in recovering encrypted files and use whatever backup copy you have of the affected files.
How does Cyberresearcher ransomware spread its malicious files(s)?
Cyberresearcher ransomware uses the most prevalent distribution method – malicious spam emails. This isn’t surprising as spam emails have become the “go-to” distribution technique used by cyber crooks in spreading malicious files of ransomware infections like Cyberresearcher ransomware. Therefore it is essential for you to be cautious emails no matter who sent them as crooks tend to disguise their emails to make them look like they were sent by well-known groups or individuals to trick users into opening the malware-laden emails.
Eliminate Cyberresearcher ransomware from your system by following the given removal guide below.
Step 1: Tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step 2: Go to Processes and look for the malicious processes of Cyberresearcher ransomware then right click on it and select End Process or End Task.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for dubious programs that might be related to Cyberresearcher ransomware and then Uninstall it/them.

Step 5: Tap Win + E to launch File Explorer.
Step 6: After opening File Explorer, navigate to the following directories below and look for Cyberresearcher ransomware’s malicious components such as the READ_IT.html file and other suspicious-looking files and then remove them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step 7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use [product-name], this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the listed paths below and look for the registry keys and sub-keys created by Cyberresearcher ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 10: Delete the registry keys and sub-keys created by Cyberresearcher ransomware.
Step 11: Close the Registry Editor.
Step 12: Empty your Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if Cyberresearcher ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Once you’re done executing the steps given above, you need to continue the removal process of Cyberresearcher ransomware using a reliable program like [product-name]. How? Follow the advanced removal steps below.
Perform a full system scan using [product-code]. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.