What is SOLO ransomware? And how does it implement its attack?
SOLO ransomware, also known as SOLO Verschlüsselungssoftware, is a data-encrypting malware discovered in the second half of October 2018. Based on its ransom note, it seems to be targeting German-speaking users although that does not necessarily mean that it can’t infect other users from other countries as well.
The instant it infiltrates a computer, it executes its malicious payload. The code of this file is configured to interfere with the important system components which in turn results in the corruption of valuable data and system settings. SOLO ransomware also downloads and creates other malicious components that it uses for its attack. These components are placed on system folders and are used for both the data gathering and stealth protection modules.
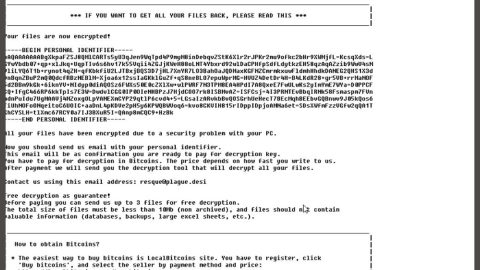
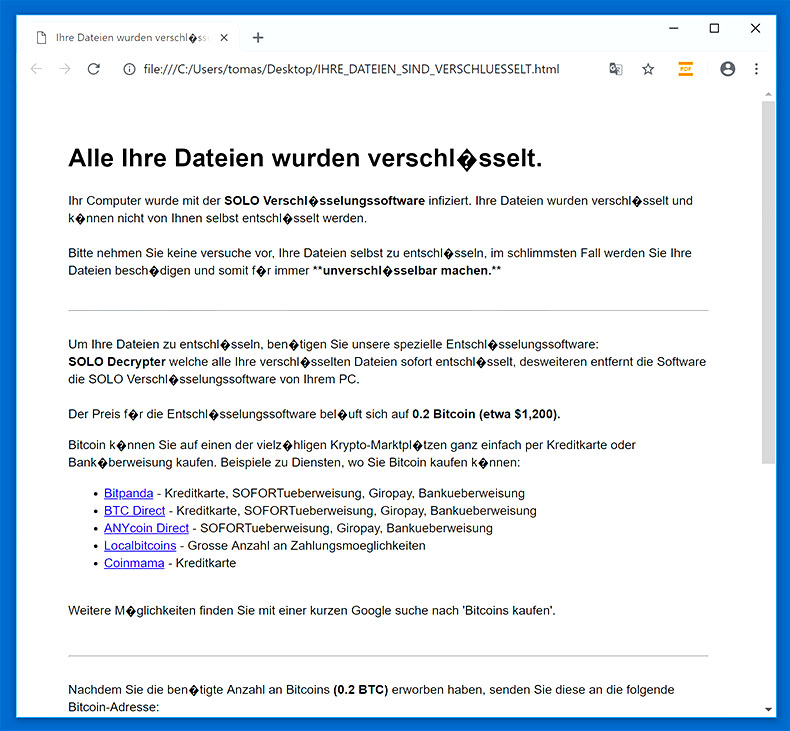
The former is used to obtain information about the infected machine and its user. The harvested data is then used for the stealth protection module which is used to keep SOLO ransomware invisible to both security and antivirus programs. Moreover, modifications in the Windows Registry are also made in order to achieve persistent attacks. And once all these changes are applied, it begins the encryption process uses the AES encryption algorithm. After the encryption, it adds the .SOLO suffix to each one of the encrypted files and drops a file named “IHRE_DATEIEN_SIND_VERSCHLUESSELT.html” which contains a ransom note written in German that states:
“Alle Ihre Dateien wurden verschlüsselt.
Ihr Computer wurde mit der SOLO Verschlüsselungssoftware infiziert. Ihre Dateien wurden verschlüsselt und können nicht von Ihnen selbst entschlüsselt werden.
Bitte nehmen Sie keine versuche vor, Ihre Dateien selbst zu entschlüsseln, im schlimmsten Fall werden Sie Ihre Dateien beschädigen und somit für immer **unverschlüsselbar machen.**
Um Ihre Dateien zu entschlüsseln, benötigen Sie unsere spezielle Entschlüsselungssoftware:
SOLO Decrypter welche alle Ihre verschlüsselten Dateien sofort entschlüsselt, desweiteren entfernt die Software die SOLO Verschlüsselungssoftware von Ihrem PC.
Der Preis für die Entschlüsselungssoftware beläuft sich auf 0.2 Bitcoin (etwa $1,200).
Bitcoin können Sie auf einen der vielzähligen Krypto-Marktplätzen ganz einfach per Kreditkarte oder Banküberweisung kaufen. Beispiele zu Diensten, wo Sie Bitcoin kaufen können:
Bitpanda – Kreditkarte, SOFORTueberweisung, Giropay, Bankueberweisung
BTC Direct – Kreditkarte, SOFORTueberweisung, Giropay, Bankueberweisung
ANYcoin Direct – SOFORTueberweisung, Giropay, Bankueberweisung
Localbitcoins – Grosse Anzahl an Zahlungsmoeglichkeiten
Coinmama – Kreditkarte
Weitere Möglichkeiten finden Sie mit einer kurzen Google suche nach ‘Bitcoins kaufen’.
Nachdem Sie die benötigte Anzahl an Bitcoins (0.2 BTC) erworben haben, senden Sie diese an die folgende Bitcoin-Adresse:
Adresse:
151oCJ1espbmqya9Vj2xxjxi1APb8zhqYR
Betrag:
0.2 BTC
Nachdem wir den kompletten Betrag erhalten haben, wird ihnen automatisch die Entschlüsselungssoftware zum Download bereit gestellt (bitte nehmen Sie keine modifikationen an dieser Datei vor, damit die ordnungsgemäße Funktionalität sichergestellt ist).
Der komplette Betrag wurde noch nicht bezahlt.
Entschlüsselungssoftware Herunterladen”
If your computer got infected with this crypto-malware, paying the demanded 0.2 BTC ransom is definitely recommended as you will only end up losing money for nothing. The best thing you can do is to obliterate SOLO ransomware from your PC and try other alternative methods to recover your encrypted files.
How does SOLO ransomware proliferate?
SOLO ransomware can proliferate using several ways. And one of the most common ways it usually uses is malicious spam email campaigns – a distribution method commonly used by ransomware developers in spreading ransomware. Crooks usually attach a corrupted link or an infected file attachment in the email. Either way, both are used to install SOLO ransomware in the system.
Obliterate SOLO ransomware with the help of the removal instructions prepared below.
Step_1: Tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step_2: Go to Processes and look for the malicious process of SOLO ransomware which may be randomly named and usually takes up a lot of CPU resources. Once you’ve found it, right-click on it and select End Process or End Task.
Step_3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step_4: Look for dubious programs that might be related to SOLO ransomware and then uninstall it/them.
Step_5: Tap Win + E to launch File Explorer.
Step_6: After opening File Explorer, navigate to the following directories below and look for SOLO ransomware’s malicious components such as “IHRE_DATEIEN_SIND_VERSCHLUESSELT.html”, <random>.exe, and other suspicious-looking files and then remove them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step_7: Close the File Explorer.
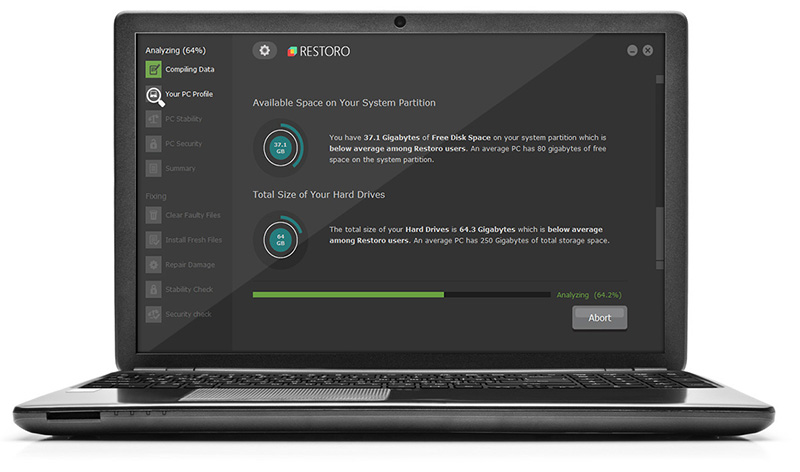
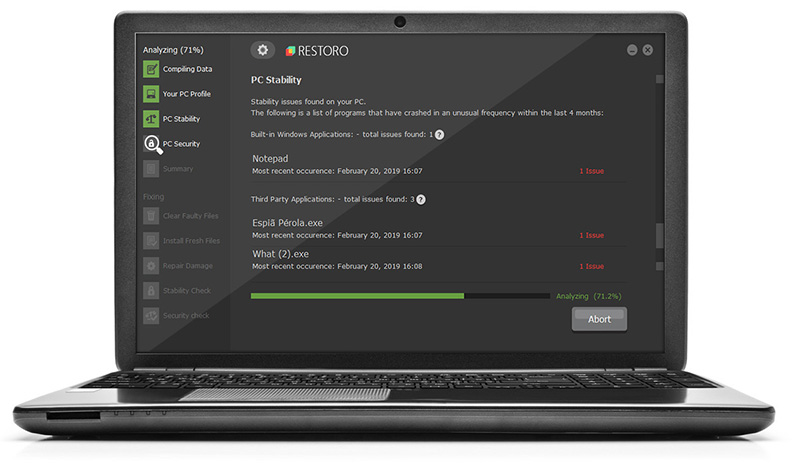
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_8: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_9: Navigate to the listed paths below and look for the registry keys and sub-keys created by SOLO ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_10: Delete the registry keys and sub-keys created by SOLO ransomware.
Step_11: Close the Registry Editor.
Step_12: Empty your Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if SOLO ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Congratulations, you have just removed SOLO Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove SOLO Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.